GetSkittled
Application Environment Manager
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
400 XP
Hey Folks, in this tutorial we are going to talk about the SearchSploit tool. This tool is specially designed for CTF players, where they can easily find the exploits with the command line.
SearchSploit
Searchsploit is a (CLI) tool for find the exploits, which also allows you to bring a copy of Exploit-DB with you. SearchSploit provides you with the ability to perform detailed offline searches in locally saved repositories. Many vulnerabilities contain links to binary files that are not included in the standard repository but can be found in our Exploit-DB binaries.
Lets do it
Installations and Updates
If you doesn’t have this tool you can download it by using the following command.
sudo apt -y install exploitdb1sudo apt-yinstall exploitdb
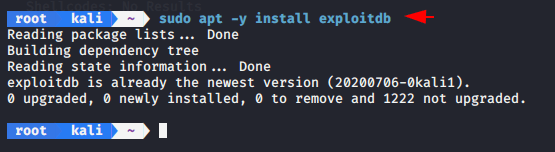
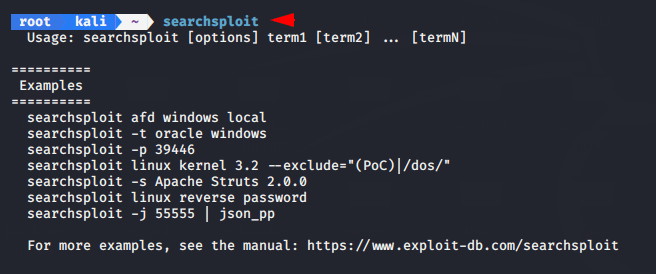
After installation is complete we can execute it from any location of our terminal.
searchsploit1searchsploit
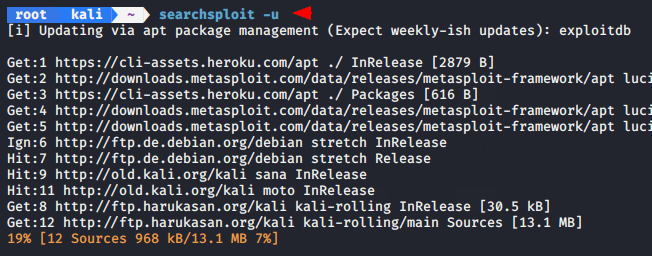
If your tool is out dated then you can use “-u” option which will automatically update your tool.
searchsploit -u1searchsploit-u
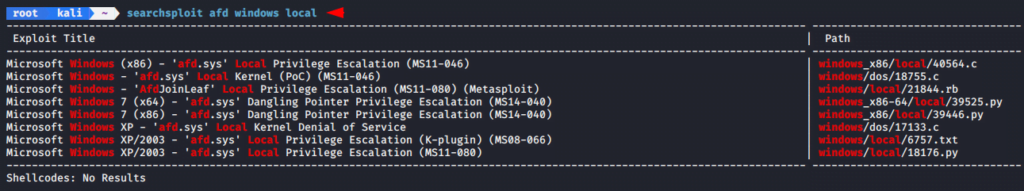
Basic search
We can just type in anything we want to see and it will give us all the results that will be related to that word.
searchsploit afd windows local1searchsploit afd windows local
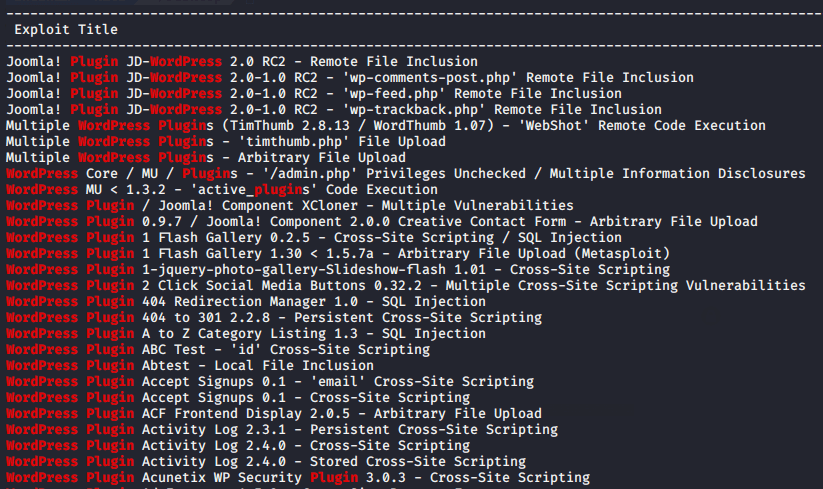
Lets take another example and try to find wordpress all vulnerable plugins.
Find Exploits
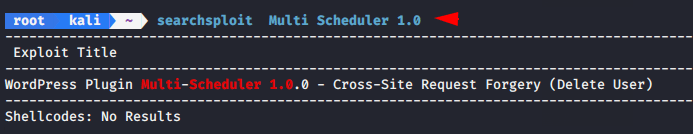
We can use the following command to get all the exploits.
searchsploit Multi Scheduler 1.01searchsploit Multi Scheduler1.0
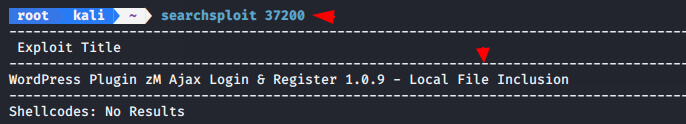
CVE
In this attempts we will try to find the exploit with CVE number.
searchsploit 372001searchsploit37200
Exploit-DB Online
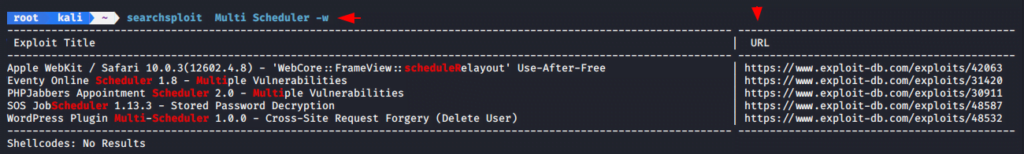
If we want to get more information about the exploits then we have to go on google to find them but by using this command we can find the exploits links directly.
searchsploit Multi Scheduler -w1searchsploit Multi Scheduler-w
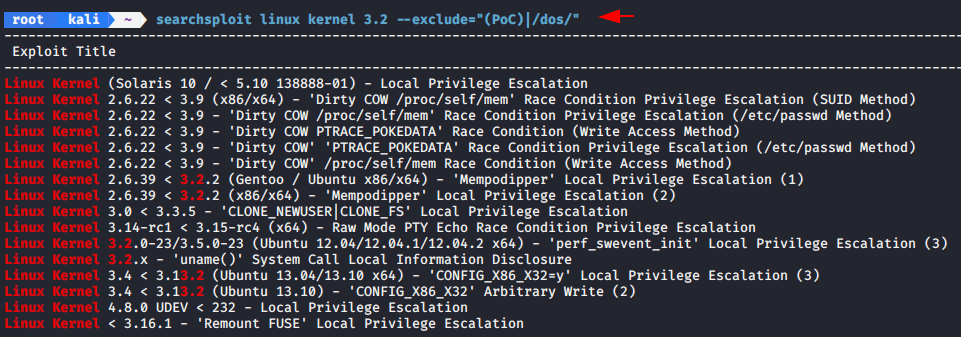
Exclude – Removing Unwanted Results
Exclude function is used to remove some unwanted results.
searchsploit linux kernel 3.2 --exclude="(PoC)|/dos/"1searchsploit linux kernel3.2--exclude="(PoC)|/dos/"
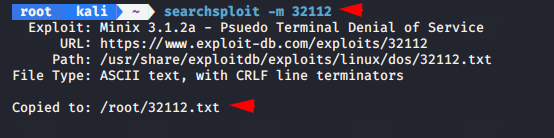
Copy To Directory
By using “-m” option we can copy the exploit in your current working directory.
searchsploit -m 321121searchsploit-m32112
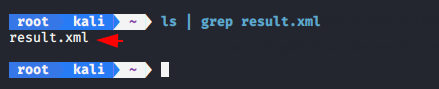
Nmap result – Find Vulnerability
Let’s figure out this feature. Now we will save our nmap results in xml format.
nmap 192.168.0.102 -oX result.xml1nmap192.168.0.102-oX result.xml
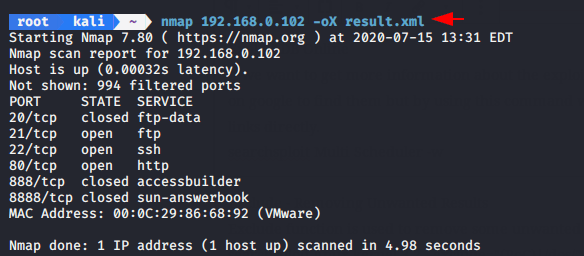
Lets check the results.
It will checks all results in nmap XML output and try to find the related exploit.
searchsploit –x --nmap result.xml1searchsploit–x--nmap result.xml
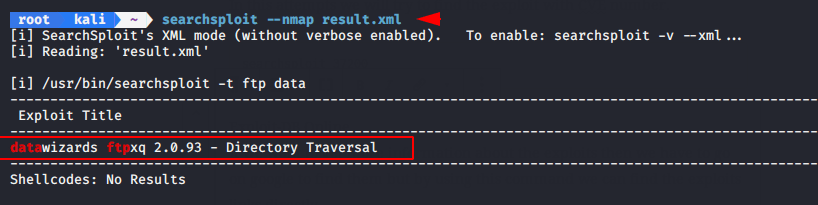
Similarly ! we can get better results by adding filters to our results.
About the AuthorShubham Goyal Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.