ggfggfgninirninw
Story Specialist
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
400 XP
Hey folks, today we are going to talk about an interesting tool called “ParamSpider“. It is extremely designed for scrap the vulnerable parameter from the web application that can be helpful during the penetration testing.
Key Features
- Finds parameters from subdomains as well.
- Finds parameters from web archives of the entered domain.
- Saves the output result in a nice and clean manner.
- Gives support to exclude urls with specific extensions.
- It mines the parameters from web archives (without interacting with the target host)
Lets do it
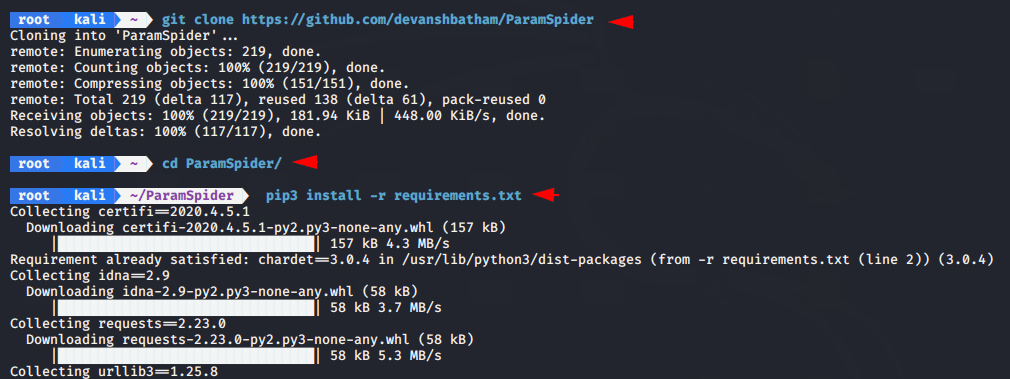
Installation
First we need to download this tool from the github page which is pretty simple, just execute the following git command and tool will be download on terminal.
git clone https://github.com/devanshbatham/ParamSpider1git clone
Loading…
github.com
Go into the directory by cd command.
cd ParamSpider1cd ParamSpider
Before start this tool we need to fulfill some requirements of this tool.
pip3 install -r requirements.txt1pip3 install-rrequirements.txt
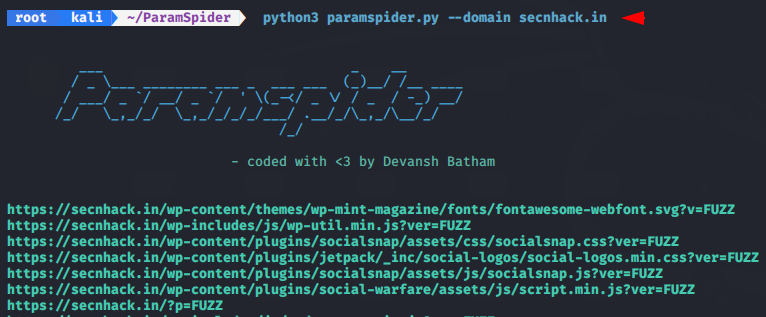
Simple Scan
Now first we will take an example without adding the filter. Through this command we will try to find all parameters in which some can be harmful or non-harmful parameters.
Usage
python3 paramspider.py --domain secnhack.in1python3 paramspider.py--domain secnhack.in
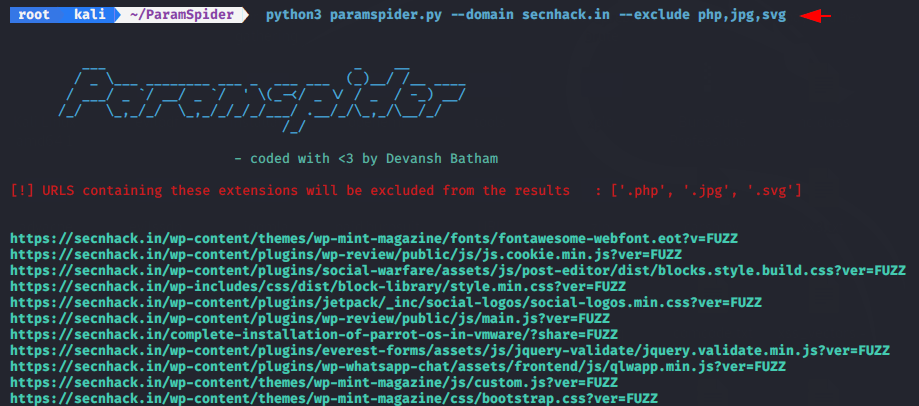
Exclude
Now we will use the exclude function of this tool to improve our results.
python3 paramspider.py --domain secnhack.in --exclude php,jpg,svg1python3 paramspider.py--domain secnhack.in--exclude php,jpg,svg
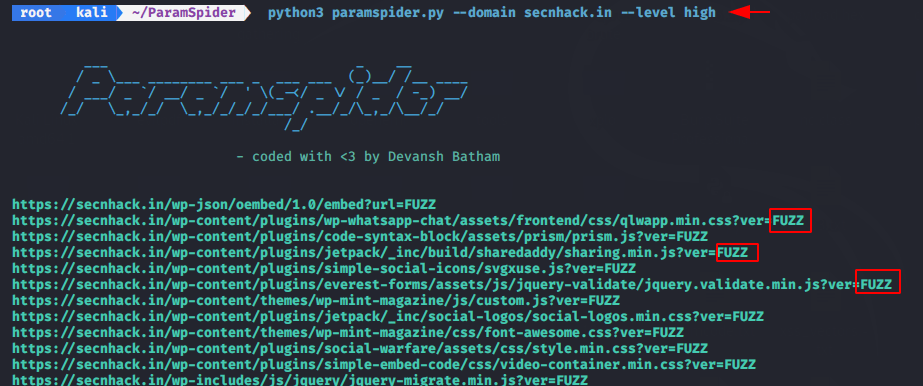
Nested
Now we will find only the nested parameter by uses the following command.
python3 paramspider.py --domain secnhack.in --level high1python3 paramspider.py--domain secnhack.in--level high
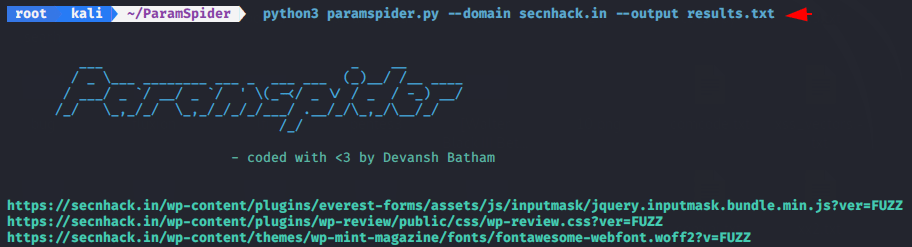
Output
We will save our results in txt file.
python3 paramspider.py --domain secnhack.in --output results.txt1python3 paramspider.py--domain secnhack.in--output results.txt
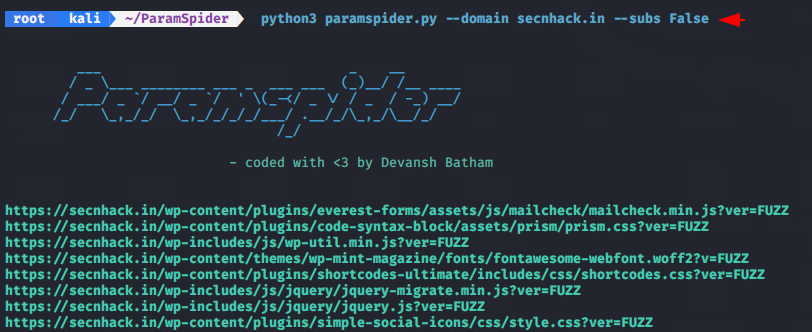
Exclude subdomains
If we do not want this tool to scan the subdomain then we can use the deprecated function of this tool.
python3 paramspider.py --domain secnhack.in --subs False1python3 paramspider.py--domain secnhack.in--subs False
Similarly, you can find unsafe parameters using this tool and after that you can start fuzzing to detect the vulnerability in the web application.
About the AuthorShubham Goyal Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.