RRDABMW
Crypto Compliance Officer
LEVEL 1
300 XP

Hey Folks, in this tutorial we are going to talk about an interesting tool called “Maryam“. Maryam is an Open-source intelligence(OSINT) and Web-based Footprinting optional/modular framework based on the Recon-ng core and written in Python. If you have skill in Metasploit or Recon-ng, you can easily use it without prerequisites and if not, then you can read the full article till the bottom.
Let’s take a look
Installation
To fully configure it you have to follow the same steps that we did. So first we will download this tool using git command from gitub, after downloading we will go to the directory and execute the “pip” command to install all dependencies.
git clone https://github.com/saeeddhqan/Maryam.git
cd Maryam
pip install -r requirements.txt123git clone
https://github.com/saeeddhqan/Maryam.gitcd Maryampip install-rrequirements.txt
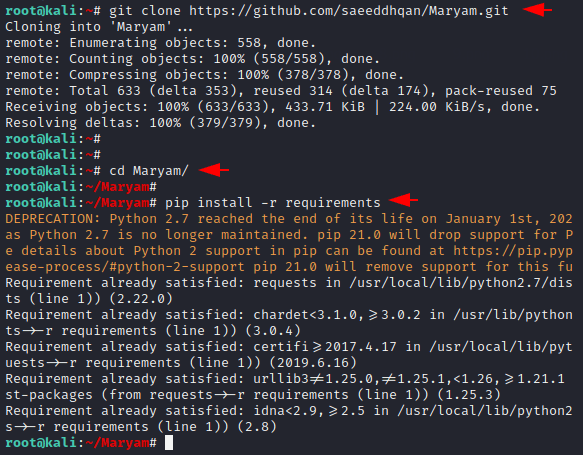
Done
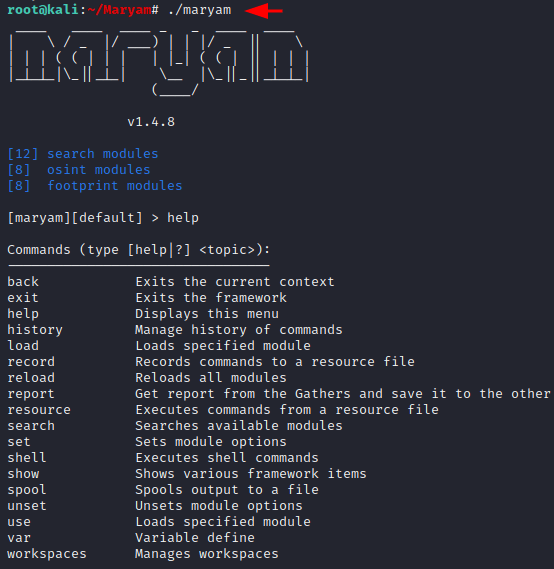
./maryam1./maryam
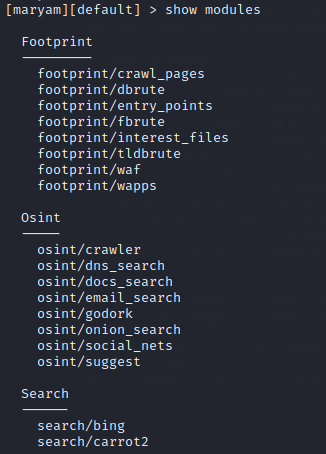
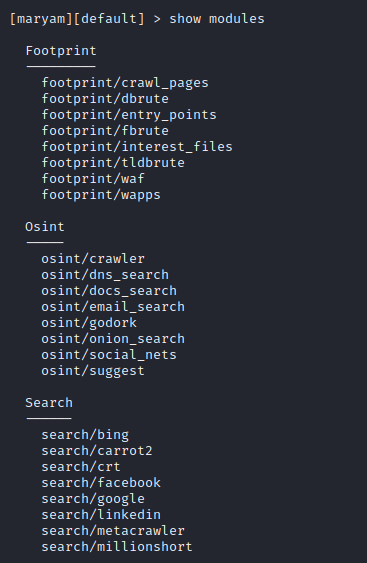
Modules
It is very easy to see all the available modules in this tool because all you have to do is execute the following command.
show modules1show modules
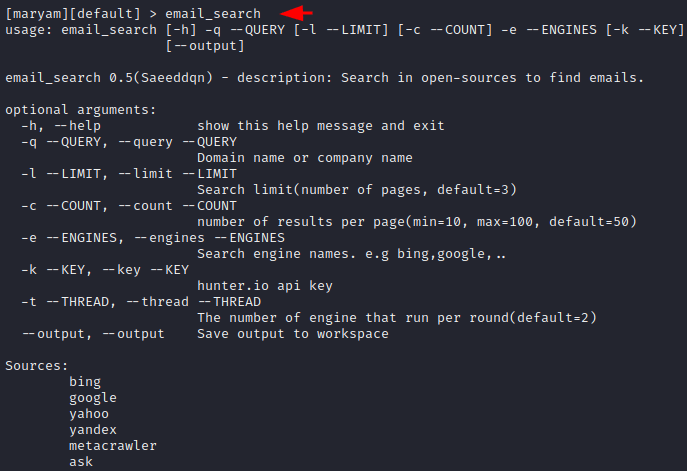
Anonymous Email Grabbing – OSINT
Suppose if you want to grab some email addresses and it does not depend who they are, you can use this option. Just you need to enter the module name and it will give you all usage details.
email_search1email_search
See below, in which the “-q” argument is queries and the “-e” argument is being used for search engine purposes. Just entered the details as per need and execute the command.
email_search -q gmail.com -e bing,google,yahoo --output1email_search-qgmail.com-ebing,google,yahoo--output
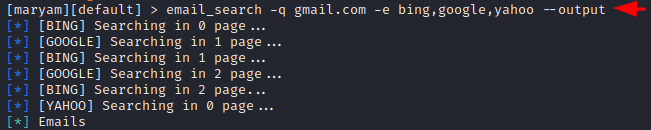
Great
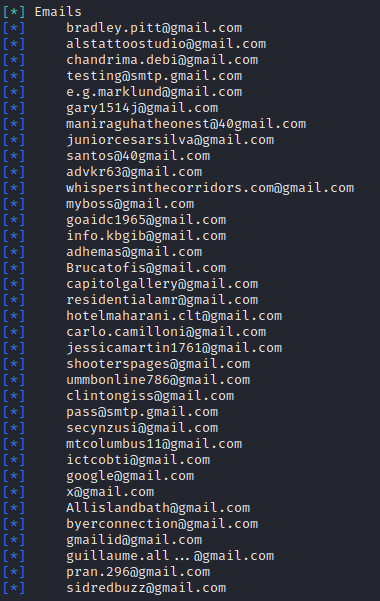
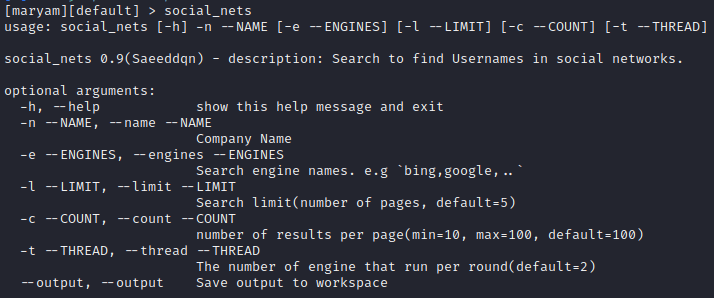
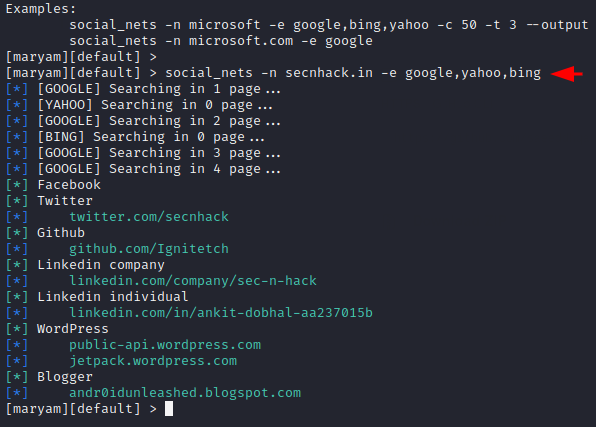
Social Nets – OSINT
This is another module related to OSINT and is used to derive a description of the target’s social media handlers. Just execute the following command to get usage of this module.
social_nets1social_nets
Hmm
social_nets -n secnhack.in -e google,yahoo,bing1social_nets-nsecnhack.in-egoogle,yahoo,bing
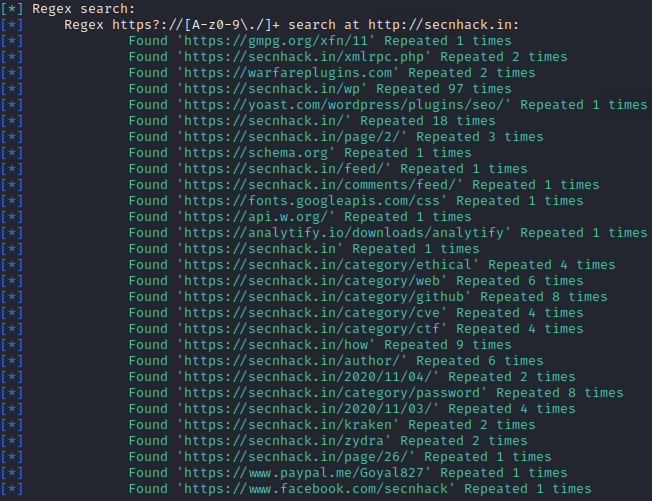
Crawl Pages – Footpriniting
Now we will adopt a footprint module of this tool. The following module has been given to crawl the entire web pages of live website. You can see the usage guide by using the following command.
crawl_pages1crawl_pages
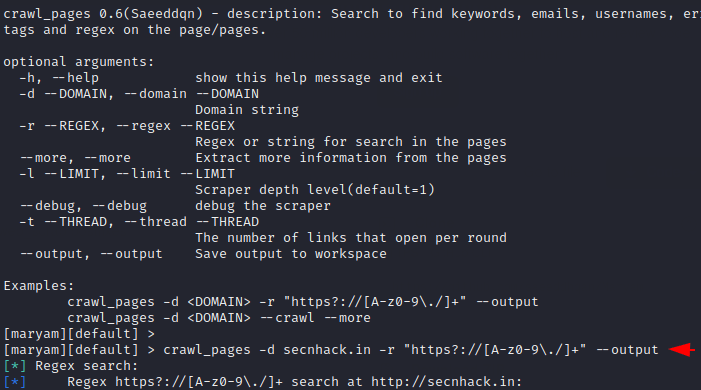
BOOM
crawl_pages -d secnhack.in -r "https?://[A-z0-9./]+" --output1crawl_pages-dsecnhack.in-r"https?://[A-z0-9./]+"--output
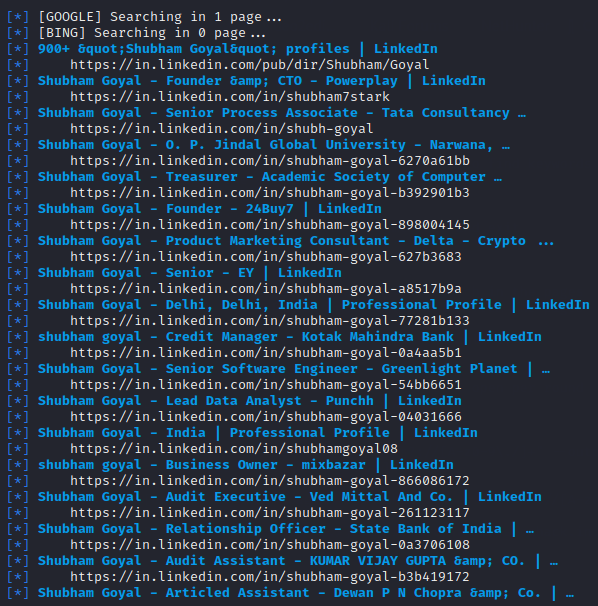
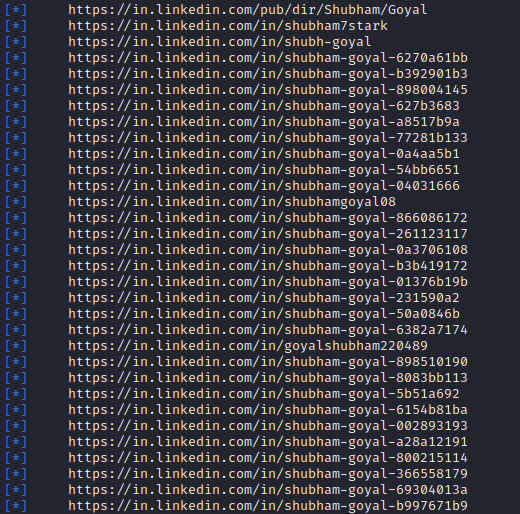
Getting Profiles From LinkedIn – Search
These can be very useful features for everyone as we often keep trying to find people’s profiles on LinkedIn one by one, but through this feature we can grab profiles of multiple people at the same time.
linkedin1linkedin
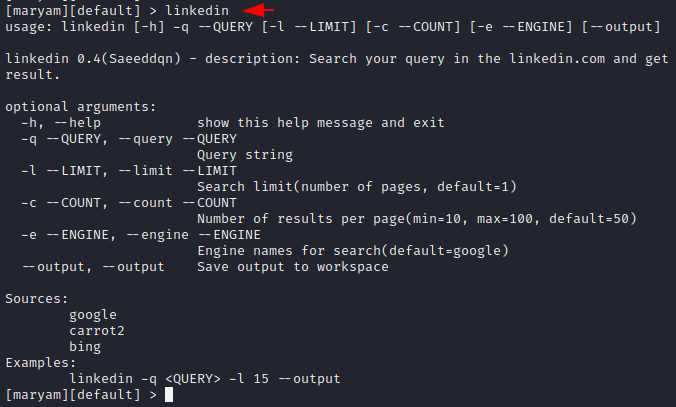
Nice
linkedin -q shubhamgoyaloscp -e google,bing,yahoo1linkedin-qshubhamgoyaloscp-egoogle,bing,yahoo
Read More …..
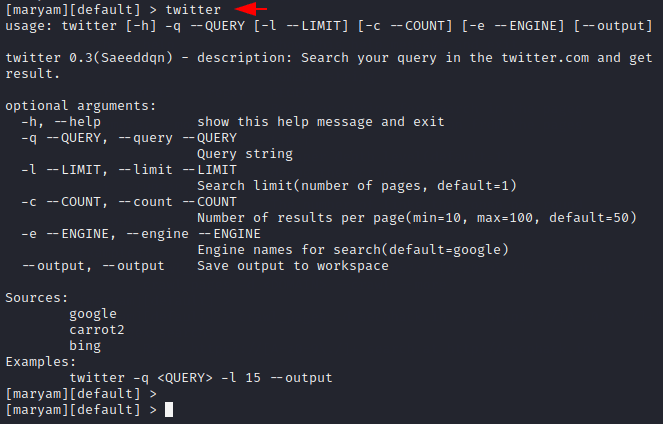
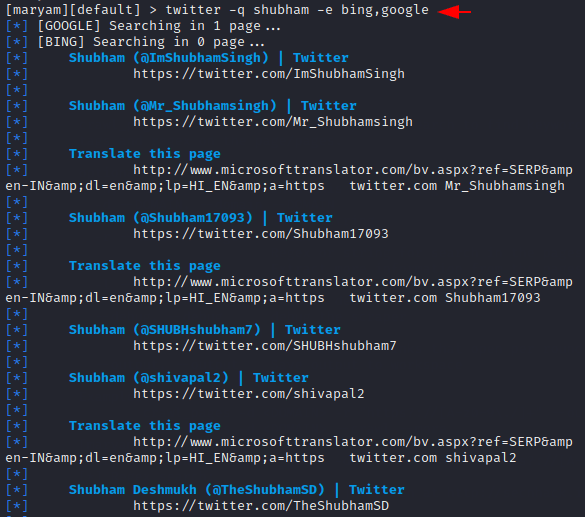
Getting Profiles From Twitter – Search
Likewise, we try to dump twitter profiles associated with this specific name listed on google, bing etc. Execute the following command to check the usage guide of this module.
twitter1twitter
Great
twitter -q shubham -e bing,google1twitter-qshubham-ebing,google
Similarly, you can use all the modules of this tool one by one and improve your information gathering skills.