fingerz003
Clown Prince
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
300 XP

Hey Folks, In this tutorial we are going to talk about “hackerenv” github tool that will helps to find and exploit the vulnerability automatically.
About the hackerEnv ?
hackerEnv is an automation tool that quickly and easily scan ports, vulnerabilities and exploit them. After exploit it hands you an interactive shell for further testing. It generates HTML and docx reports. It uses other tools such as hydra, nmap, nikto, metasploit and works in kali linux and Parrot OS.
Lets take a look
Installation
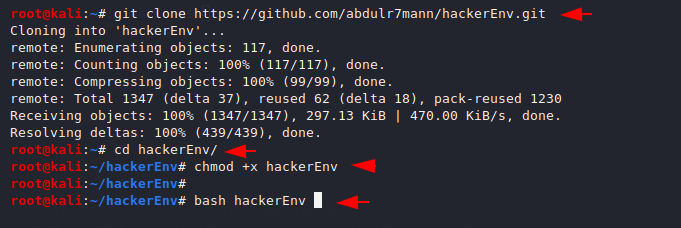
First we have to download this tool from gitub page with git command. After installation we have to give some permission by going to the directory after which we can run this tool.
git clone https://github.com/abdulr7mann/hackerEnv.git
cd hackerEnv
chmod +x hackerEnv
bash hackerEnv1234git clone
https://github.com/abdulr7mann/hackerEnv.gitcd hackerEnvchmod+xhackerEnvbash hackerEnv
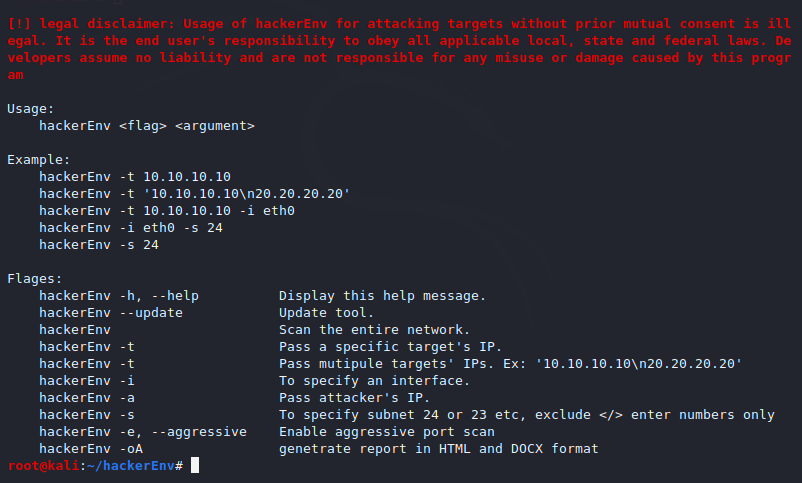
Help
Here is the help command with which we can see the features of the tool.
bash hackerEnv -h1bash hackerEnv-h
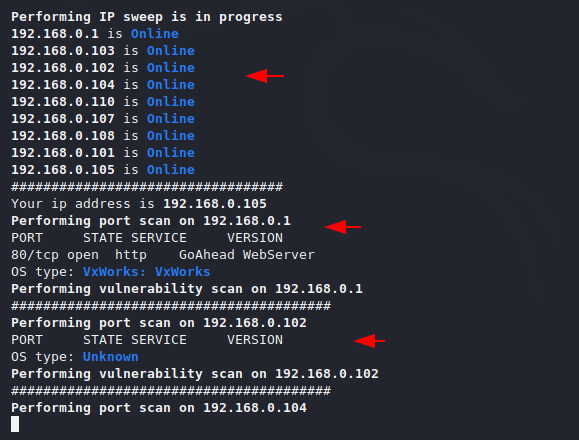
Active IP Address
These features can be useful for beginners. After executing the given command it will provide the result of how many IP addresses are activated or assigned.
bash hackerEnv1bash hackerEnv
Example
For an example or testing we will use our vulnerable machine. Now we will give this tool the IP address of the vulnerable machine. After providing the IP address, it will automatically find the open ports.
bash hackerEnv -t < ip address >1bash hackerEnv-t<ip address>
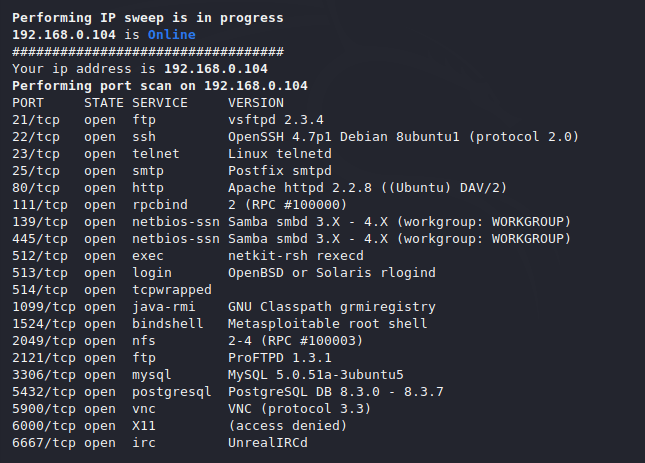
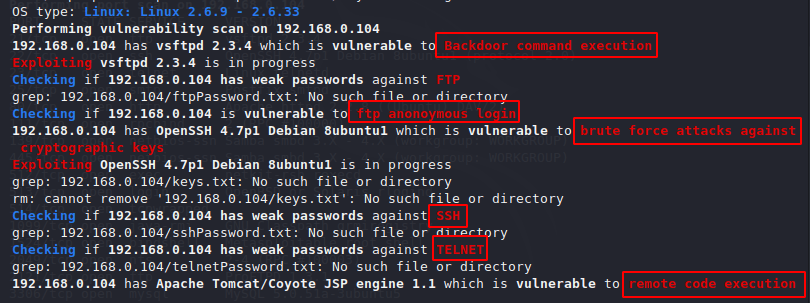
As you can see it has given us the details of open ports and their vulnerability, after which we can exploit vulnerabilities with the help of any search engine or SearchSploit tool. Also you can see that the command execution vulnerability is on the webserver which we can take advantage of and remotely control.
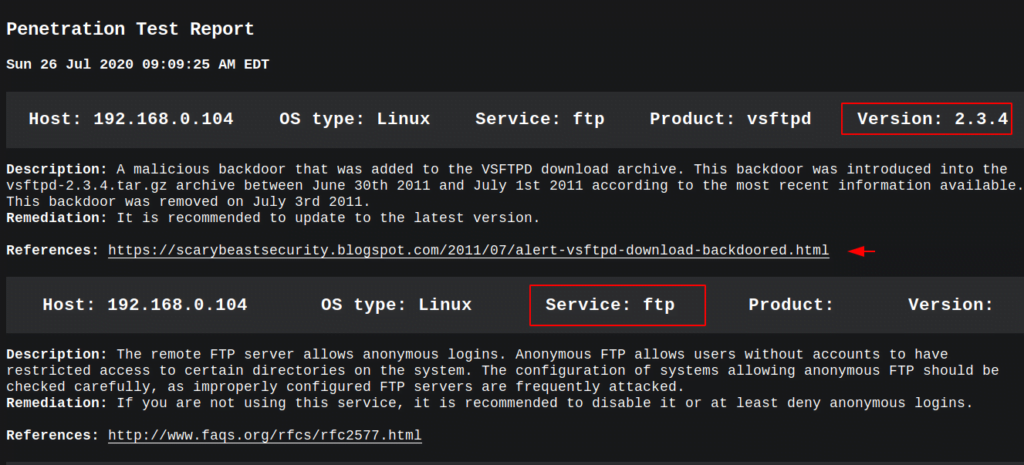
As we mentioned above, it saves the result in HTML format, which we can see from here.
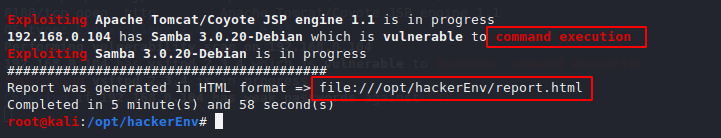
Now we can see the results in depth and it also provides reference to the exploits from which we can go directly to the website.