damieral019
Cybersecurity Architect
2
MONTHS
2 2 MONTHS OF SERVICE
LEVEL 1
400 XP
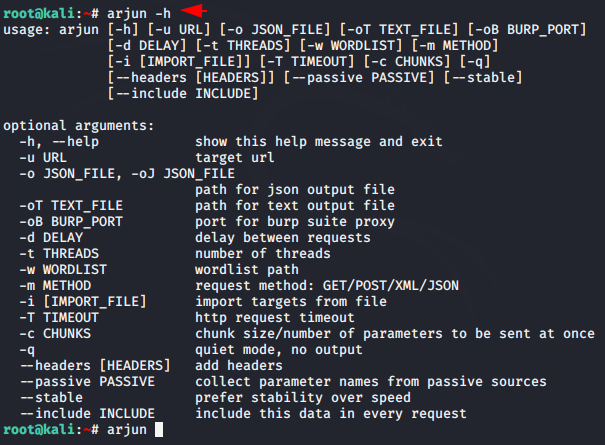
Hey Folks, in this tutorial we are going to talk about another bug bounty tool called “Arjun“. The Arjun tool is specifically designed to find query parameters for URL endpoints. It finds valid HTTP parameters with a huge default dictionary of 10,985 parameter names. The best part of this tool is that it takes less than 10 seconds to go through this huge list while making just 20-30 requests to the target.
Let’s take a look
Configure Dependencies
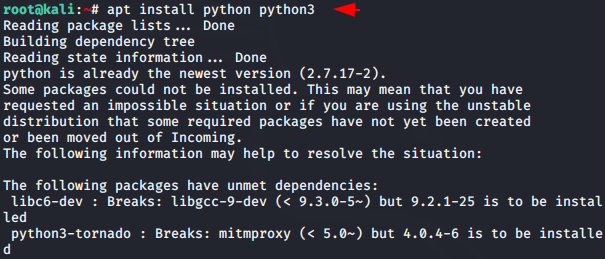
Now this tool comes pre-installed but only in the latest release of kali linux, so we will try to install it by ourselves. The tool is coded in python language which is why we need to install python compiler to operate this tool.
apt install python python31apt install python python3
Move
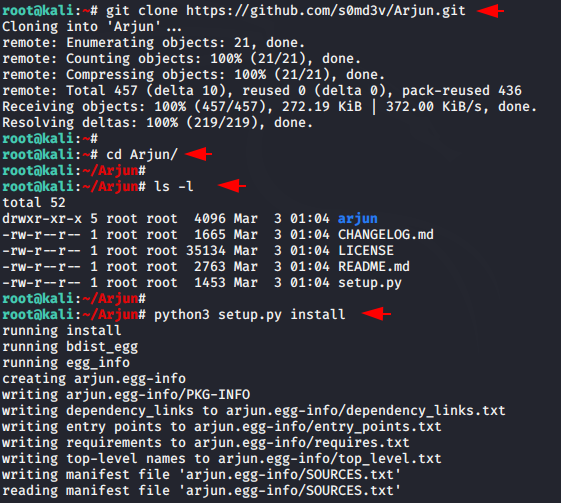
git clone https://github.com/s0md3v/Arjun.git
cd Arjun
ls -l
python3 setup.py install1234git clone
https://github.com/s0md3v/Arjun.gitcd Arjunls-lpython3 setup.py install
COOL
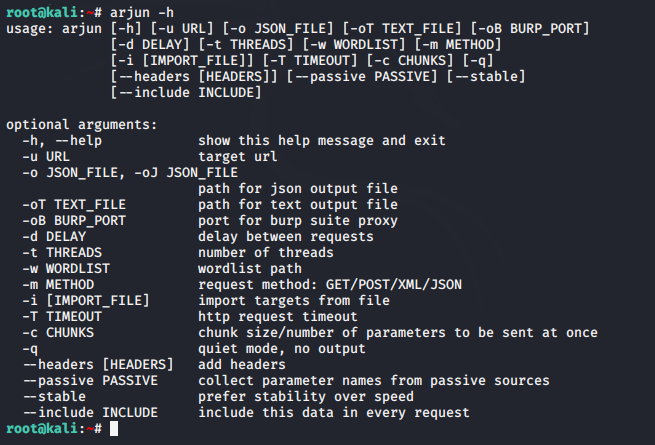
arjun -h1arjun-h
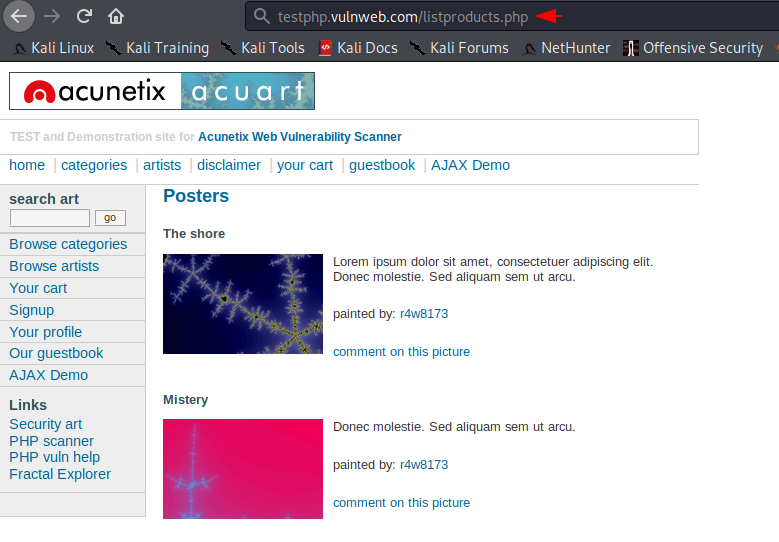
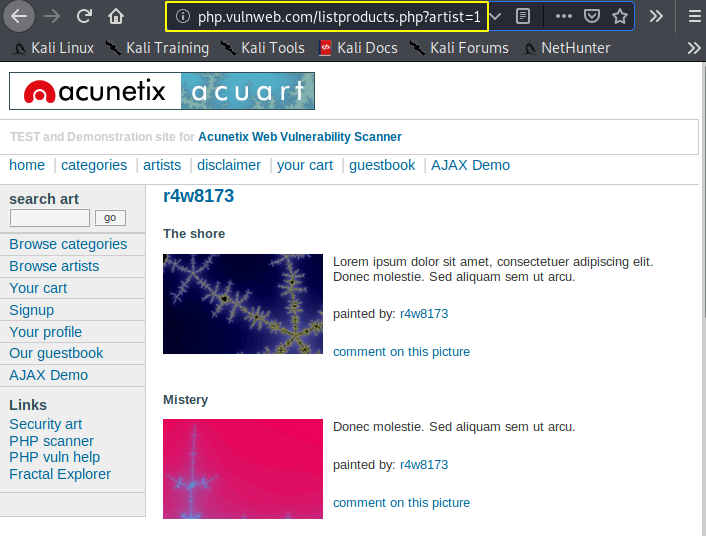
Let us show a demo of this tool. As you can see in the image below, there is no parameter available to give input in URL. Let’s try to explore valid parameter.
Loading…
testphp.vulnweb.com
Loading…
testphp.vulnweb.com
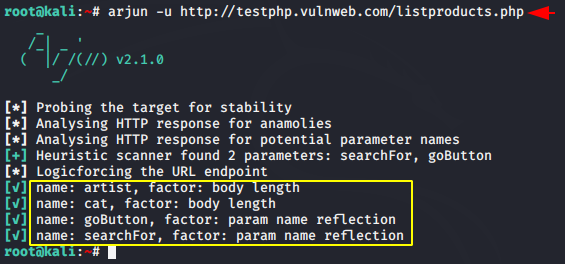
All you have to do is name the target URL and wait until the scan is complete. After the scan is complete it will show all valid parameters. Let’s take it one of those valid parameters.
arjun -u http://testphp.vulnweb.com/listproducts.php1arjun-u
Loading…
testphp.vulnweb.com
Valid
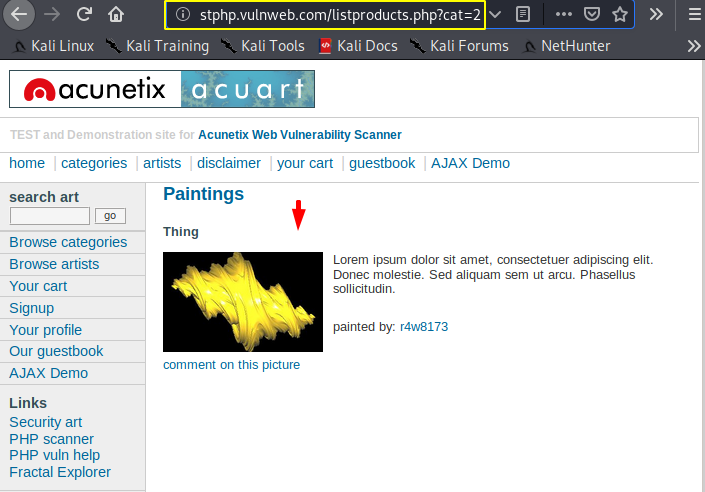
Good
Save (JSON)
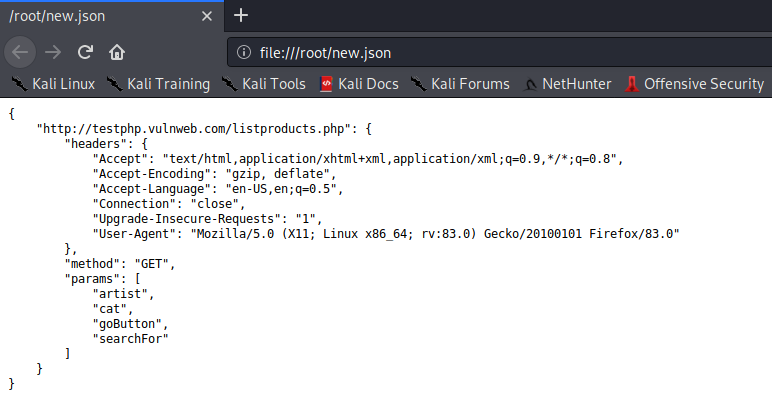
We can present the entire result in JSON file format using the following command.
arjun -u http://testphp.vulnweb.com/listproducts.php -o new.json1arjun-u
http://testphp.vulnweb.com/listproducts.php -o new.json
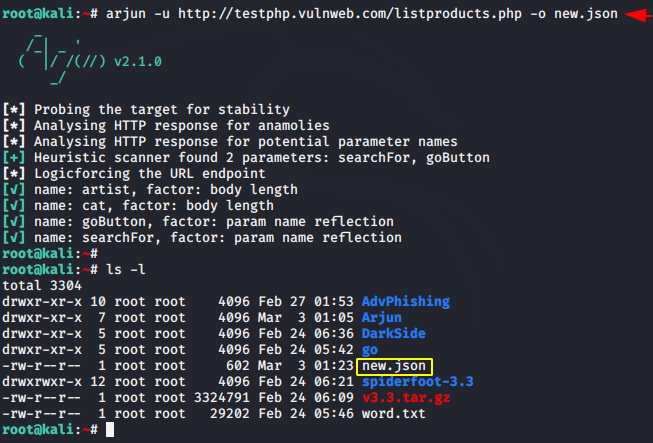
Done
The main features have been presented to you and you can try the rest one by one yourself.