riperdood
Blockchain Security Consultant
LEVEL 1
400 XP
Hey Folks, in this tutorial we are going to configure a prominent vulnerability assessment tool called “Nessus“. Nessus is a remote security scanning tool, which scans a computer, web application and if it detect any vulnerability, it raises the alerts. Nessus provides additional functionality beyond testing for known network vulnerabilities. For instance, it can use Windows credentials to examine patch levels on computers running the Windows operating system.
Let’s take a look
Download Software
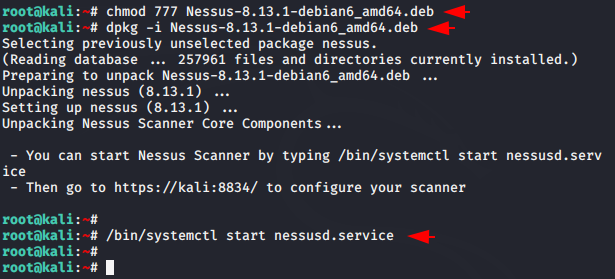
Definitely, this tool will not spend your bandwidth much because we will install it through the deb file. Download deb file for linux but according to the architecture. Keep in mind, it does not depend which OS you are using because you can configure this software in any debian system using the following command.

Once you have downloaded the deb file, place it to your favorable directory, give the executable permissions and install the Nessus.deb file using the dpkg command. Once all steps are completed, start the service.
chmod 777 Nessus.deb dpkg -i Nessus.deb
/bin/systemctl start nessusd.service12chmod777Nessus.deb dpkg-iNessus.deb/bin/systemctl start nessusd.service
Ready
Loading…
localhost

Great

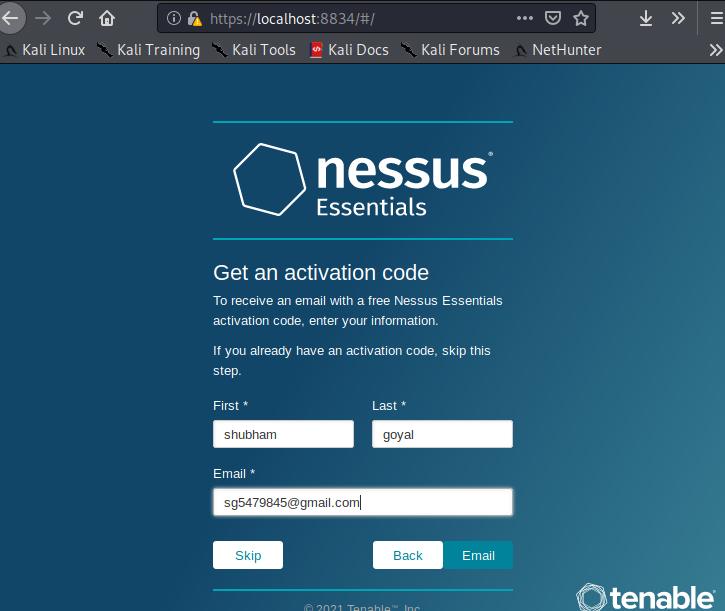
Now here we enter some necessary personal details to verify ourselves.
Hmm

Now we need to provide unique username and password to secure the admin account.

Really

HUREE
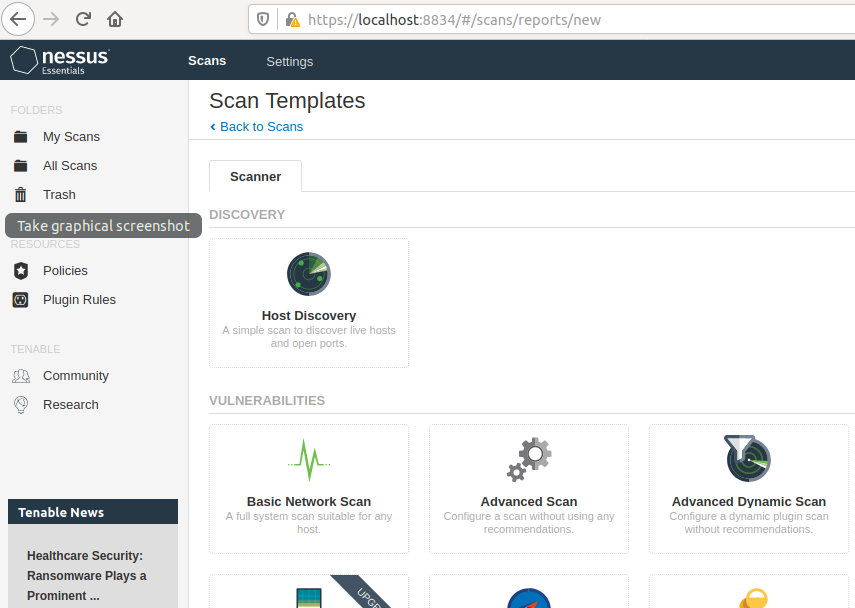
After getting hold over this tool, you can easily make any changes in the account settings.

Wait
About the AuthorShubham Goyal Certified Ethical Hacker, information security analyst, penetration tester and researcher. Can be Contact on Linkedin.